Microsoft & Google Accounts in the Crosshairs
By: Jim Stickley and Tina Davis
April 3, 2026
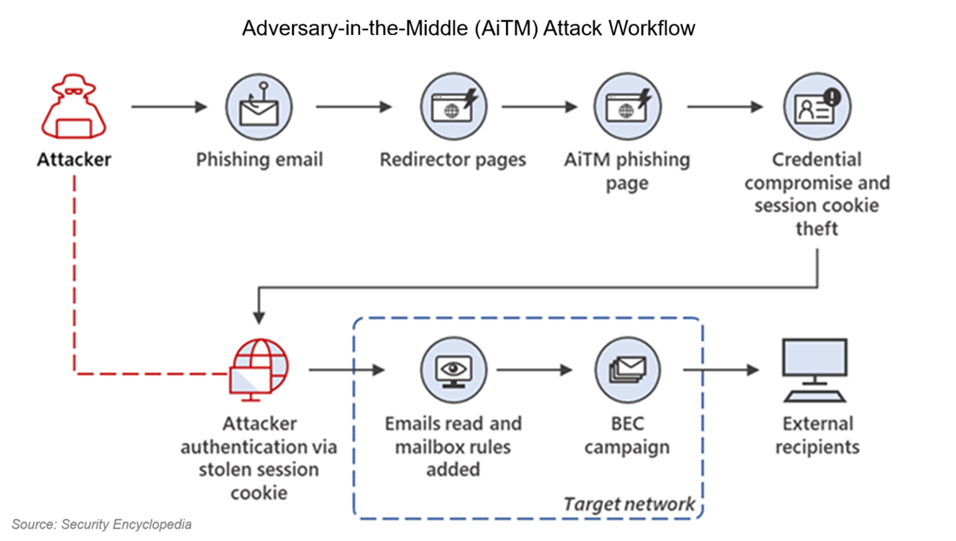
An uncovered phishing-as-a-service (PhaaS) operation called VoidProxy is making waves in the cybersecurity world, and not in a good way. Researchers report that this scheme is designed to steal login credentials, multi-factor authentication (MFA) codes, and even session cookies from services like Microsoft and Google. If it’s successful, VoidProxy can slip past many of the protections we all think are keeping us safe.
Criminals are sending phishing emails through legitimate but compromised email marketing services such as Constant Contact or Mailchimp. Since these messages come from trusted providers, they’re more likely to sneak past filters and into inboxes. The links inside are often disguised through URL shorteners and multiple redirects, sometimes hidden behind CAPTCHAs or hosted on cheap, disposable domains. If a victim enters credentials on a spoofed login page, VoidProxy captures everything in real time and uses it to hijack the session.
So, what can you do? Experts stress the importance of moving to phishing-resistant authentication like hardware keys or passkeys, which cannot be intercepted in the same way as codes. Organizations should also tighten access policies by restricting sensitive accounts to trusted devices or networks and monitoring for unusual login behavior.
On the individual side, being skeptical of emails with shortened links or urgent demands remains critical. If it makes you feel rushed, that’s when you should take more time to think about whether or not it’s worth it to click a link. If it’s really a matter of life or death, you’re more likely to receive a phone call.
VoidProxy is proof that attackers are working harder to bypass defenses. Staying informed and layering protections are the best ways to avoid becoming their next victim.