ClickFix Attacks Help You Hack Your Own PC
By: Jim Stickley and Tina Davis
March 15, 2026
PC users beware—ClickFix attacks are here. Global cybersecurity company ESET’s did some research on the topic. Its research finds ClickFix incidents are now a close second to phishing—and that’s saying something. They also found these two-faced attacks multiplied a crushing 500%+ during that same year. And they are pretty crafty in their trickery too.
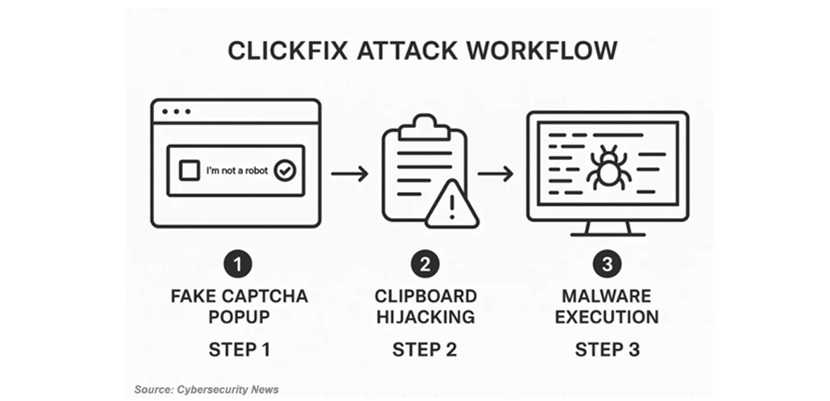
ClickFix attacks trick you into hacking your own PC.
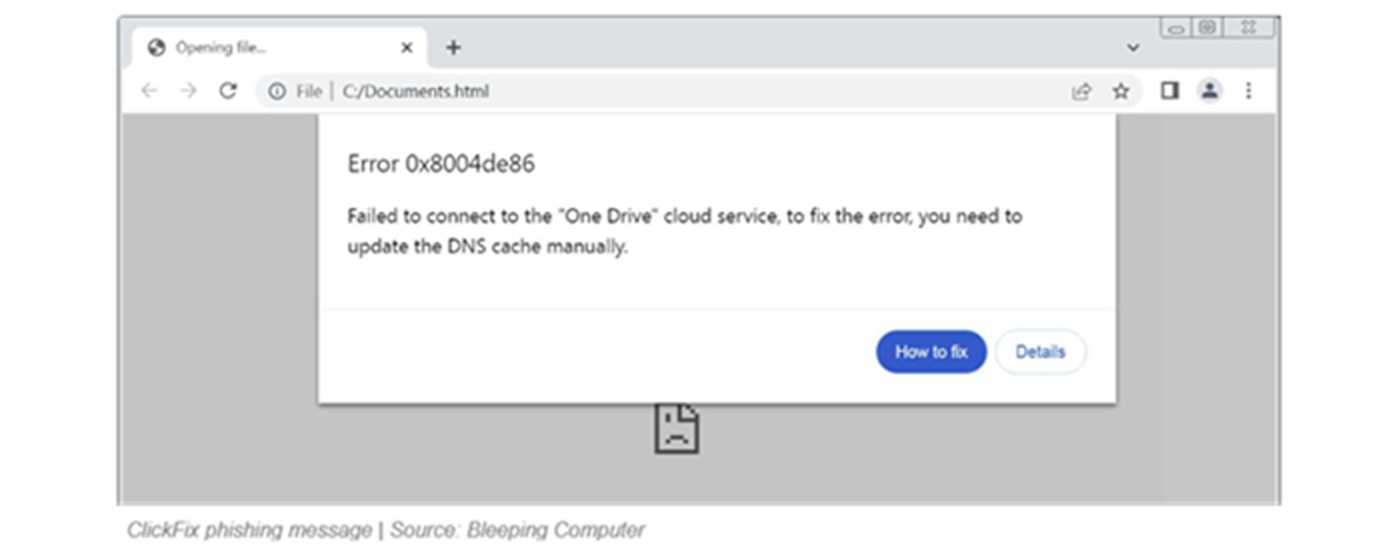
These attacks begin with phishing emails, phishing websites and fake reCaptcha’s. Taking the bait results in an “error message” on your device. Even more alarming, the message also tells a victim “You’re the only one who can fix it.” Once you take the bait, you’re also told the following steps will “fix the security error.” Unfortunately, those directions won’t ever fix the security error. That’s because there never was an error to begin with. Instead, what it means is the victim just handed their self-hacked PC to the attacker.
Spotting A ClickFix Strike
Keeping your phishing cyber-smarts set on high helps avoid ClickFix and other phishing attacks. Knowing a setup when you see one also goes a long way for safety. If there’s one particular thing to look for with ClickFix attacks no matter how it’s delivered or worded, there’s always a hacker message or direction to:
Press the Windows Key + “R” and then paste “Ctrl+V” then “Enter.”
Whatever you do, don’t do it! If you do, you’ll end up doing the hacker’s job for them.
It’s well known that over 90% of cyberattacks begin with phishing. It’s been an invaluable hacking tool for decades since phishing tactics keep reinventing themself as technology marches on. These attacks are getting more sophisticated by the day, and with help from AI there’s no telling what’s next.
ClickFix is one of the latest episodes in the long line of phishing attacks aiming to catch us off guard. And since we don’t know what’s coming at us next, keep your phishing red flags waving and never take the bait.