Malware is quickly making its way into 2019 and it’s taking no prisoners. From IcePick-3PC to ServHelper to FlawedGrace and they are not stopping at any organization’s external defenses. These all are currently active, along with others, and most of the time, they find their way into a network or onto your computer via phishing. And they are even helping each other out to maximize efforts.
ServeHelper is one that should be on the radar of everyone. It has been around since the end of 2018 and its primary goal now is to open up a backdoor on Windows PCs so that TA505, the hacking group behind it, can walk in and help themselves to your data.
But, ServHelper doesn’t stop with that. It also lends a helping hand to FlawedGrace. This group of malware has been around since November 2017. Researchers at Proofpoint have explained some of the detail surrounding this collaboration of malware, but suffice it to say the basics of detecting phishing attacks are really important to protect against this one-two punch.
Both rely on phishing. Most of it is via massive spam campaigns, as opposed to specifically targeting individuals, groups, or industries. It counts on the unwitting victims, curiosity, and our propensity to open attachments and click links without much thought.
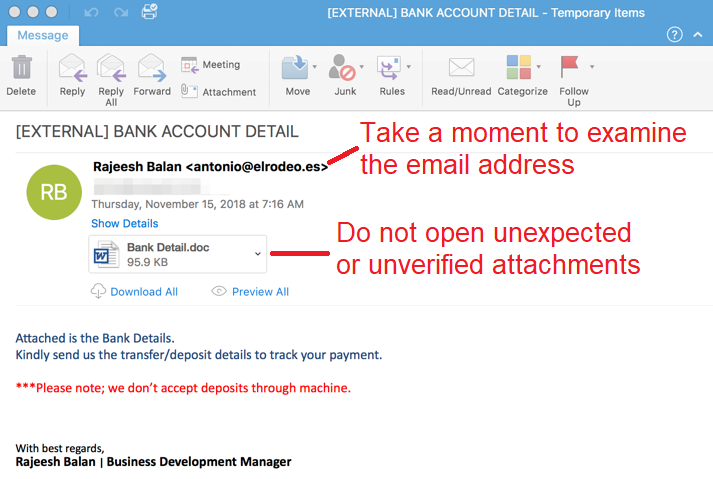
Don’t be one of those victims. If you are not expecting a link or attachment, don’t open it. It’s really that simple. If there is a hint of a threat in an email (which phishing email often employ), don’t click. And if there is any doubt what so ever that an email may be phishing, your instinct is probably correct.
Don’t make any sudden movements. Take some time to think about what the messages is saying and remember that if something truly is urgent, the sender will contact you in such a way that has more chance of catching you…such as on the telephone. If it’s in an email, whatever the situation is, can wait a bit.
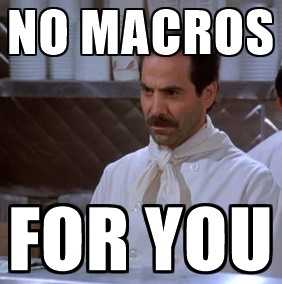 In this ServHelper attack, an attachment is sent that requests the enabling of macros. There really is no need to enable macros unless you created them or you know who did. These are generally disabled by default, but you should definitely go into the settings of your Microsoft Office products and make sure they are not allowed without asking first. If an attachment does request these, close it and contact the sender to make sure those are truly needed and that he or she did intend to send that attachment.
In this ServHelper attack, an attachment is sent that requests the enabling of macros. There really is no need to enable macros unless you created them or you know who did. These are generally disabled by default, but you should definitely go into the settings of your Microsoft Office products and make sure they are not allowed without asking first. If an attachment does request these, close it and contact the sender to make sure those are truly needed and that he or she did intend to send that attachment.
If you let this malware in, the attackers have remote access and can get your user account information, web profiles, and pretty much whatever they want to find.
FlawedGrace, on the other hand, can take full control of a device it infects. It often does target financial institutions and retailers. It wants your online banking credentials to send to the attackers.
Researchers think there is even another malware campaign being operated by the same TA505 group and that perhaps all of these are being run alongside each other. Possibly this is to make them less traceable and detectable. Be cautious. Don’t help them out.