That's A Big Oops! Medical Data Emailed to Wrong Recipients
By: Jim Stickley and Tina Davis
December 2, 2018
Over 8,000 members of FirstCare Health Plans found emails containing their sensitive information were sent to someone else’s inbox. Earlier this month, the Texas-based healthcare company notified plan members that automated email reports with their personal health information (PHI) were emailed to the wrong address–for over 17 months. This comes on the heels of both Aetna and CVS direct mailings that exposed the HIV status of individuals through the envelope windows.
The Beazley Q3 Breach Insights Report finds accidental exposures account for 32% of all healthcare data breaches, with outside hacks and malware incidents at 30%. These results show the biggest threats to healthcare data breaches are the organizations themselves. At a time when healthcare organizations are facing more data breaches than ever, many are wondering why these avoidable mistakes are being made.

The emails of 8,056 FirstCare members were not encrypted and had both PHI and personally identifiable information (PII) like member names and ID numbers, treatment descriptions, provider, and authorization numbers. The FirstCare IT department discovered the error and removed the incorrect recipient from the email distribution list, followed by a full review of other automated messaging to ensure similar errors did not occur. FirstCare has taken several steps to contact the user of the email account and secure the PHI. Emails were sent to the account to get the user to make contact, but those attempts failed. FirstCare then engaged the U.S. Federal Government to investigate and help identify the owner of the email account to minimize the potential for harm.
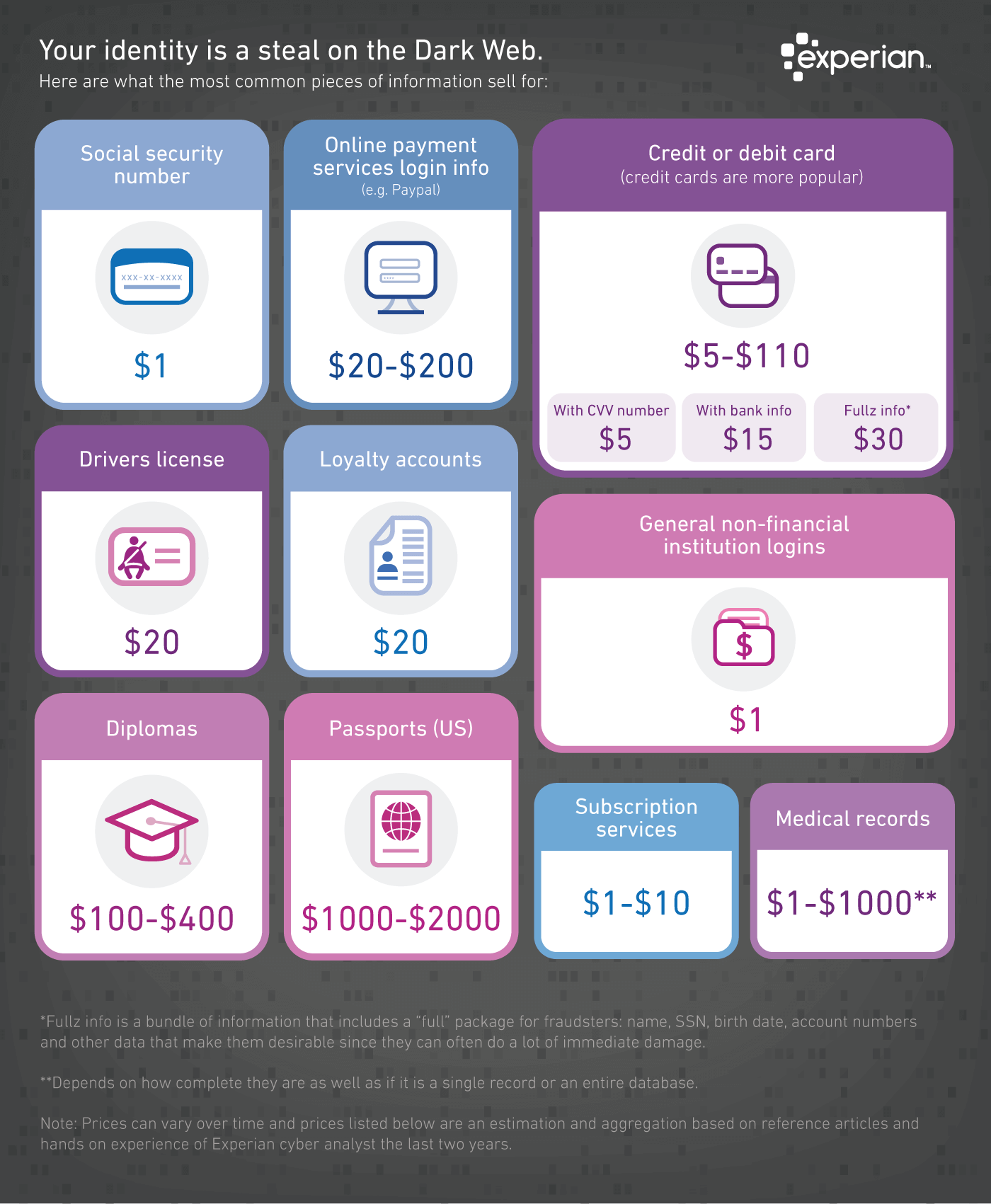
Email automated lists should be audited on a regular basis when PHI or PII is involved. This information sells for a pretty penny on the dark web and although most people just toss it aside rather than use it for black market profit, some will most certainly take advantage of these types of errors.
However, the biggest mistake is sending PII and PHI in email in the first place. Email really should be considered an unsecure form of communication. While encrypted information can indeed protect in some cases, it only works if both sides use that encryption. In many instances, this is not the case. Therefore, instead of putting it in email, let the recipient know they should log into their account to retrieve that type of information in their secured mailbox.
Although FirstCare claims there is yet no evidence showing the misdirected PHI was used for harm, only time will tell. It does bring to light just how easily mistakes are made by healthcare organizations that inadvertently exposes patient PHI in ways that should have been avoided. Employee errors need to be minimized, especially when the result could be the exposure of PHI for countless healthcare patients. Cybersecurity education as an ongoing effort is an important base for employees to safely move forward in their jobs–with the attention to detail that’s sorely needed to protect PHI. Unfortunately, the current state of healthcare data breaches shows “the call is coming from inside the house.”