Phishing email can be so realistic that it can catch out even the most technically savvy of us. And because Microsoft Office 365 is so popular in the business world, attackers tend to use it as a vehicle for various phishing attacks. Lately, a recent attack is sent in email as a PDF document that is linked to an Office 365 phishing page. That page impersonates a law firm in Denver, CO. Think to yourself, should you land on an unfamiliar page..."Why would my Office 365 link go there?"
Netskope Threat Protection posted in a press release about this attack which is difficult to detect even for those who are accustomed to checking for the “https” and the lock icon on web pages, because it is hosted on a Microsoft Azure blob storage server. It had an actual Microsoft-issued SSL certificate and domain. These facts made people trust it more and therefore, they felt OK clicking on it.
Unfortunately, people entered their Office 365 credentials into a fake page. No document was downloaded, but the attackers got their information.
There were many more steps to this scam, but these few shown steps will give you enough to know so you can avoid being a victim:
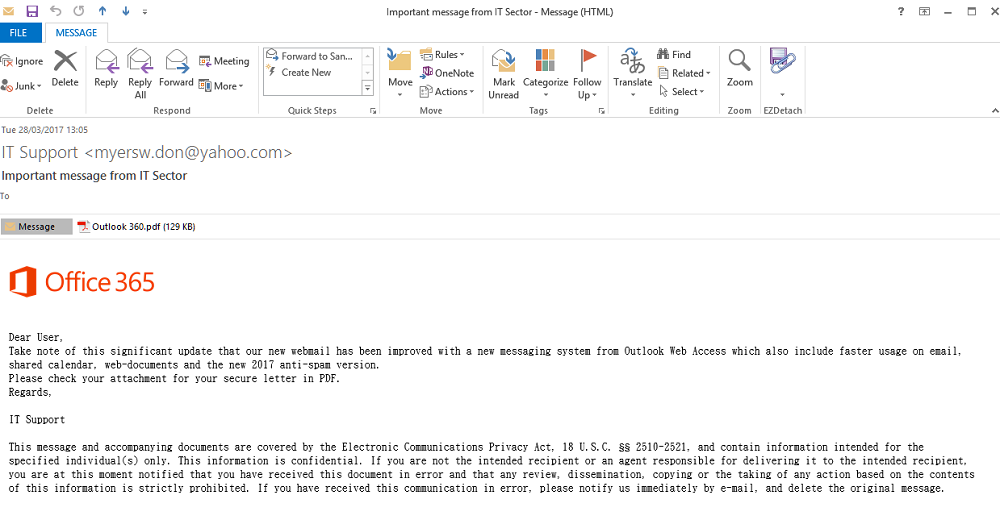
1. Phishing email sent with .pdf attached:
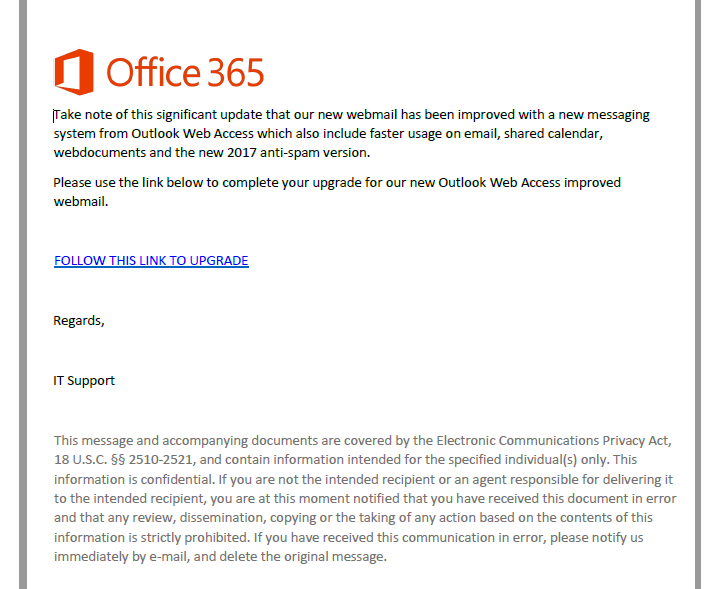
2. The attached .pdf has an embedded link that if clicked, will take you to a fake site:
3. Fake website that captures your login credentials:

For those who may not have heard of it before, Azure blob storage is a way to store massive amounts of unstructured data in the cloud that is hosted by Microsoft. That made it really hard to notice. The Microsoft name was really in the URL. And in this case, since the security certificate was actually issued by Microsoft, it was easy to fool people.
 However, there was a way to detect it as phishing. That is from the subdomain, which was the Azure blob storage. Office 365 is actually on an official Microsoft domain, rather than the Azure subdomain. In other words, “Azure” wouldn’t be in the name. Go ahead now. Look at your Microsoft Office 365 link and see what it is. Be sure to know what the address is for your Office 365 and whenever you need to enter credentials, go to a bookmark that you know is safe rather than clicking on links in email messages.
However, there was a way to detect it as phishing. That is from the subdomain, which was the Azure blob storage. Office 365 is actually on an official Microsoft domain, rather than the Azure subdomain. In other words, “Azure” wouldn’t be in the name. Go ahead now. Look at your Microsoft Office 365 link and see what it is. Be sure to know what the address is for your Office 365 and whenever you need to enter credentials, go to a bookmark that you know is safe rather than clicking on links in email messages.
However, also remember that if you are not expecting a link or attachment, don’t click on it. If you have any doubt at all about the legitimacy of an email, contact the sender by phone or by paying a personal visit before clicking. Don’t reply to the email sent or use information sent in the email. Find the contact information some other, trusted way.
For organizations, be sure to implement and keep updated all antivirus and antimalware tools. Keep those perimeter security tools up-to-date too and ensure all servers are properly configured.