Just weeks after a data breach, especially a mega breach like Target and Equifax, it looks like you may have survived unscathed. After all, you’ve checked your credit report and changed your login information for the breached company. If your data really was used against you, you’d surely know about it by now, right? Well, maybe not.
The reality is, hackers hold onto stolen data as long as they like before using it, or maybe even never use it. They know that after a breach, those affected consumers will be on the lookout. That’s why many hackers hold onto the “stolen goods” until a breach is long forgotten. In reality, keeping track of data breaches is itself a tall order. Mega breaches are publicized, but there are plenty that go unnoticed. If only doing the right thing after a breach were enough to keep safe from being exploited.
Trend Micro points out “Theft of user credentials might even be more dangerous than PII (Personally Identifiable Information), as it essentially exposes the victim’s online accounts to potential malicious use…Email is often used to verify credentials and store information from other accounts, and a compromised email account can lead to further instances of fraud and identity theft.” In other words, a hacker will leverage your stolen information to do even more damage. A pilfered contact list can lead to many spin-off crimes, especially socially engineered phishing attacks–also called spear phishing.
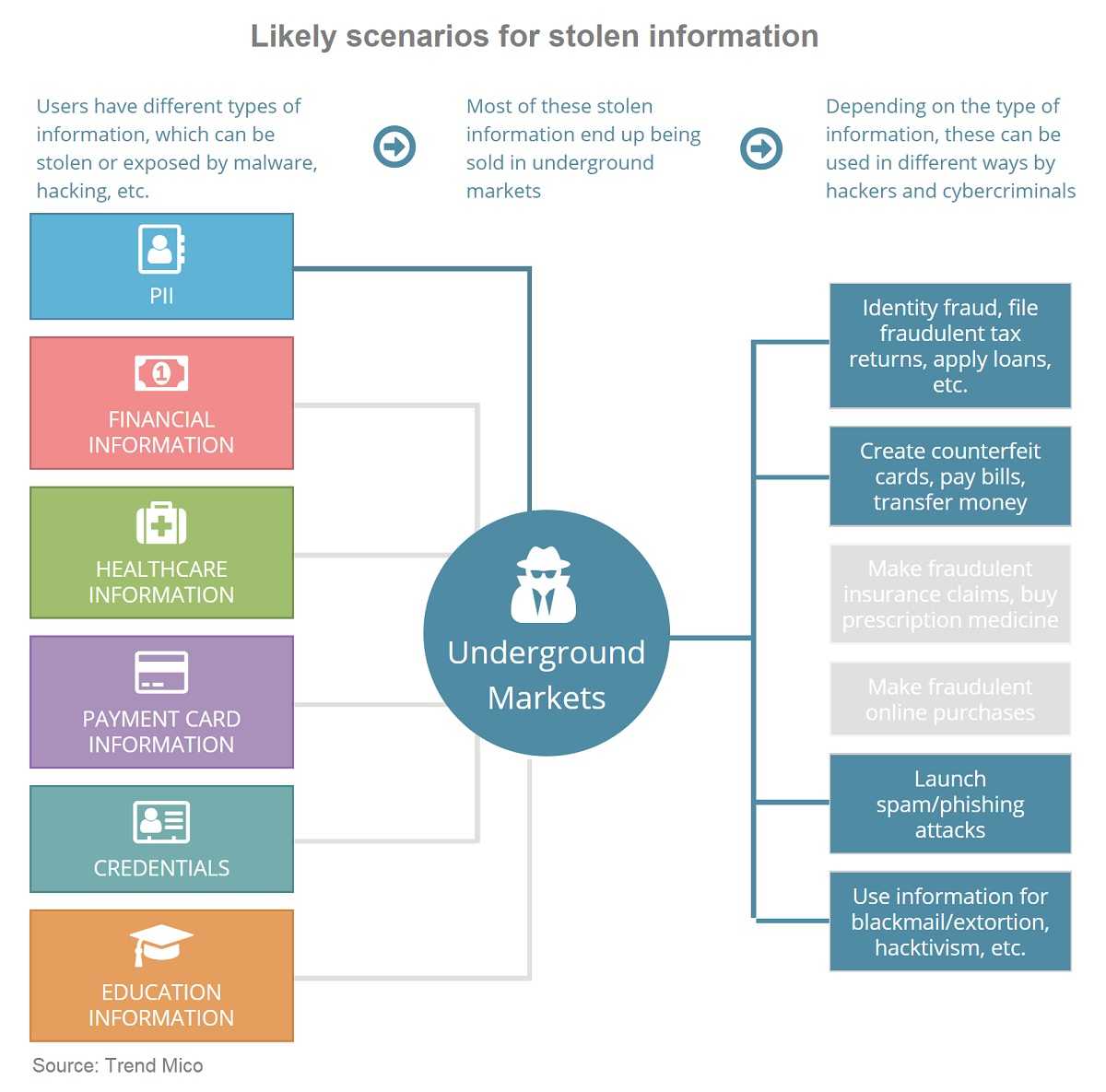
Selling stolen data on the Dark Web is another option for hackers. When that happens, your data ends up in the hands of who knows who, to do who knows what with it. The going rate for personal data on the Dark Web can be hard for a hacker to resist. Online payment credentials go for $200, and passports are worth up to $2,000 each. Maybe not much on their own, but a breach that claims thousands of payment credentials or passports adds up quickly when for sale. In the case of breached health care provider, not only are patient files full of PHI (Protected Health Information) selling for $1,000 per file, but medical providers often store patient payment information–an added bonus for hackers.
Using stolen data for phishing attacks is very appealing to those who have it. In one case, a compromised employee email account was used to send 10,000+ socially engineered phishing emails. When hackers have first and last names and personal interests, the phishing emails are even more effective. Every bite on a phishing lure provides even more contacts for further attacks.
 Always independently verify links or attachments that arrive in email messages that you are not expecting even if you recognize the sender, are from unknown senders, or just make those hairs stand up on the back of your neck. There is a reason that happens and you should listen to it.
Always independently verify links or attachments that arrive in email messages that you are not expecting even if you recognize the sender, are from unknown senders, or just make those hairs stand up on the back of your neck. There is a reason that happens and you should listen to it.
Staying vigilant on a daily basis is a prerequisite for staying safer online, especially after being involved in a data breach. Remember, long after a breach has been forgotten, it’s time for patient and persistent hackers to get to work.