Emotet Banking Malware Infection Process
By: Jim Stickley and Tina Davis
May 15, 2019
Malware is getting so complex that it’s becoming more and more difficult to detect using various security tools. Recently, researchers at Check Point found that the Emotet Trojan, first discovered in 2014 is surprisingly persistent and continues to evolve and hang around. While it initially focused on stealing financial information, it has now become a force to be reckoned with. It has a whole repertoire of methods to infect networks, including via exploit kits, network shares, and the tried and true spam email campaigns.
Emotet Infection Process:
Step 1 - Email received containing a document link
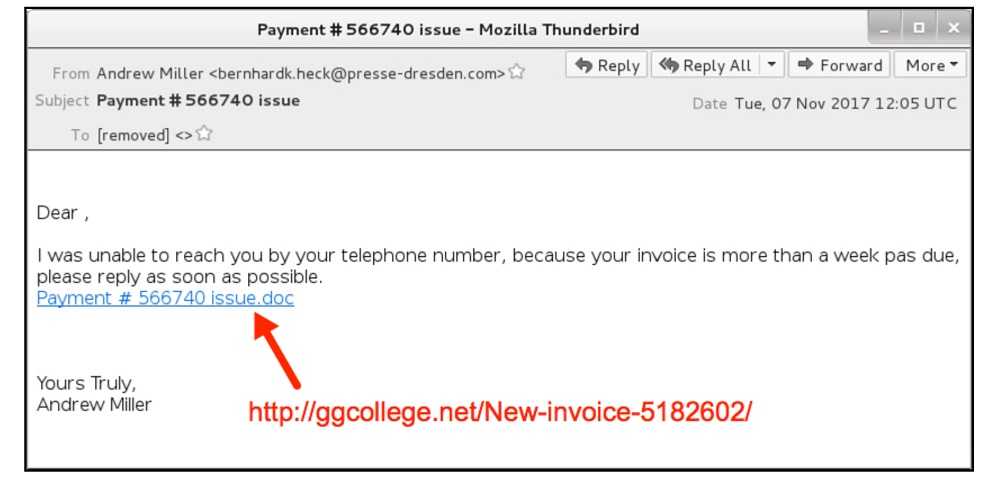
Step 2 - User clicks the link and is directed to a malicious website
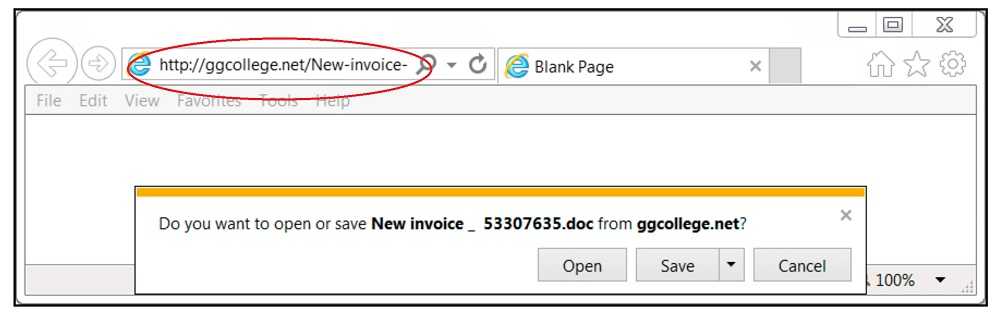
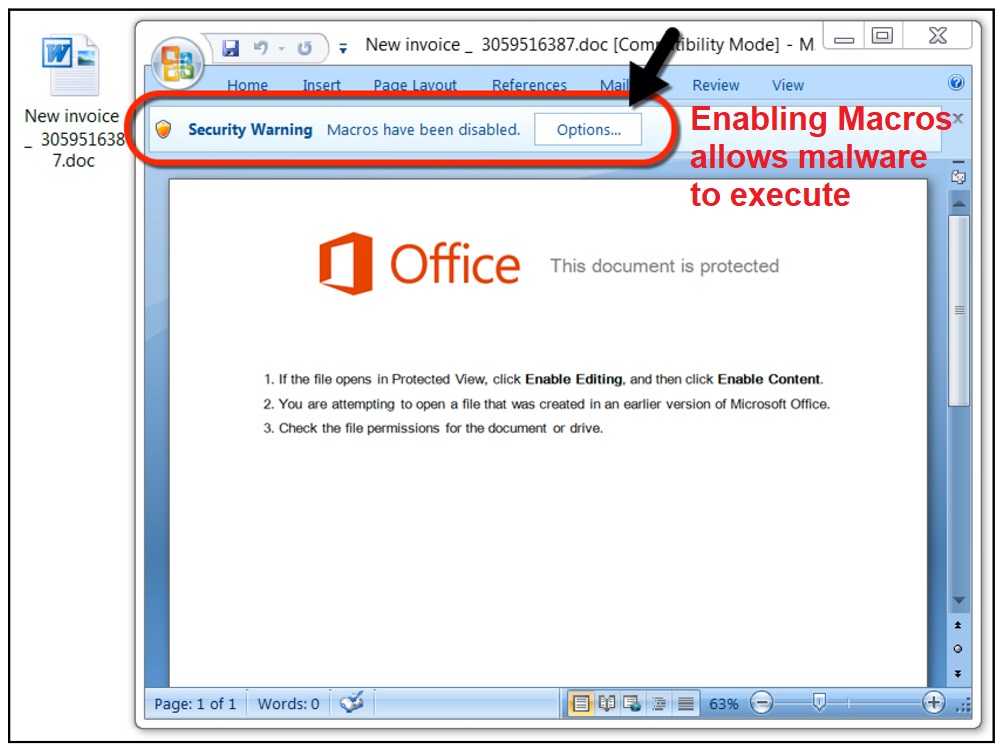
Step 3 - User downloads malicious document; if macros are enabled the malware is executed
The researchers found that Emotet can now upgrade itself to the latest version of the malware once it lands on a network. It also can rotate through command and control servers to send the information it collects making it difficult to detect. As a result of these changes as well as others, US-CERT issued a bulletin informing us that this Trojan has cost various government organizations $1 million per incident, on average.
 How do you protect against this and others like it? Cybersecurity awareness and training for everyone on the network. No matter how many tools are in place to detect spam, phishing, malware, etc., eventually a malicious email will make it into someone’s inbox. Thorough and continual training on the latest threats and mitigation is possibly what will save your organization from Emotet and others like it.
How do you protect against this and others like it? Cybersecurity awareness and training for everyone on the network. No matter how many tools are in place to detect spam, phishing, malware, etc., eventually a malicious email will make it into someone’s inbox. Thorough and continual training on the latest threats and mitigation is possibly what will save your organization from Emotet and others like it.
And even this version of Emotet is different from previous ones. Very recently, it was also used by the hacking group Mealybug to spread another banking Trojan, Qakbot.