Anubis Malware Sneaks Into Google Play Store, Attacks Smartphone Apps
By: Jim Stickley and Tina Davis
August 2, 2019
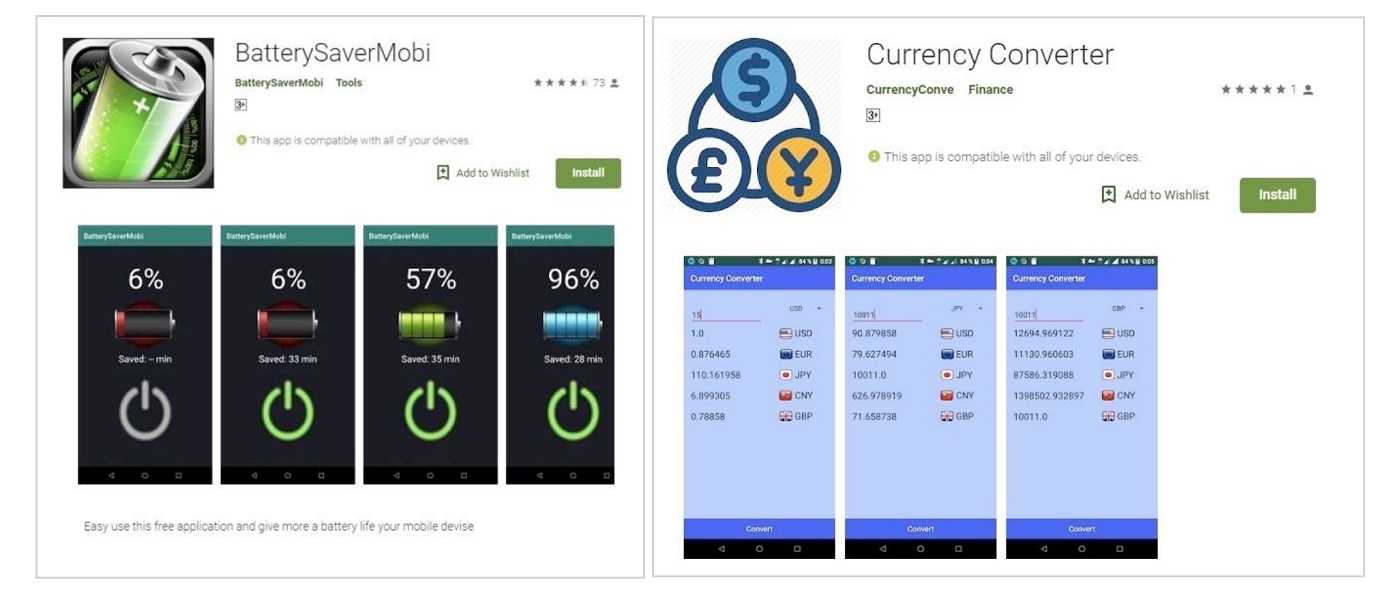
It was another malware hit for Google’s Play Store when the well-known banking Trojan, Anubis, was recently discovered living there–again. Anubis was hiding in two apps: a currency converter and a battery saver app (images below). Sounds innocent enough except…a relatively new Android banking malware, Anubis goes for the jugular by heisting banking credentials, encrypting files, recording audio, unleashing spam text messages (smishing) and scam telephone calls (vishing), and locking the user’s screen. Anubis also uses a dropper method to infect Play Store apps.
Droppers are a low cost, low-risk type of malicious script, and they’re great at hiding malware. Designed to target a system, droppers open the door by installing core malicious modules for future attacks. The combination is a one-two punch for Anubis, who is throwing the punches, and Play Store users, who are on the receiving end.
Anubis Trojan takes screenshots of a device and its built-in keylogger records keystrokes, both of which are a huge help for stealing banking credentials–all with a user having no idea their phone is under attack. Targeting app stores, especially Google Play Store and Apple’s App Store, are a hacker favorite for distributing malware to the public at large. As both app stores are aware of just what a hacking target they are, they proactively try to find it before it latches onto apps. Researchers find Anubis has ransomware features, as it was first discovered in August 2018 with the ability to encrypt files. Encrypting data with the goal of demanding a ransom payment to get the data back is a long-time ransomware tactic.
Experts believe Anubis and other malware targets smartphones because the data is less likely to be backed-up, and they are more likely to have personal photos and other valuable data that’s ripe for ransom. What do app-loving users do to keep their smartphones safe from malware? The following suggestions apply to both Android, Apple, and all other smartphone users who love their apps.
 Download directly from official app stores only. Although they might not be perfect, they’re aware of being a target for malware and they’re working on keeping the site safe. Researchers who discover tainted apps alert both app stores to the threat, an important part of having the app immediately removed before others are infected with a download.
Download directly from official app stores only. Although they might not be perfect, they’re aware of being a target for malware and they’re working on keeping the site safe. Researchers who discover tainted apps alert both app stores to the threat, an important part of having the app immediately removed before others are infected with a download.
- Sideloading apps from third-party sites is a recipe for disaster. Hackers count on users sideloading apps to disperse malware easily and without any type of oversight–think kid loose in a candy store. The money one can save by sideloading apps is hardly worth the risk of a device-takeover.
- Research an app before downloading. Read customer reviews, and beware of any reviews that appear glowing, as they are likely planted by those looking to grab as many downloads as they can. Also, check the number of downloads versus how many glowing reviews there are. Don’t be surprised if the number of reviews is much larger than the actual number of downloads–a major clue something isn’t right.