Microsoft Wins Prize For Most Used Attack Vector By Cybercriminals
By: Jim Stickley and Tina Davis
July 31, 2018
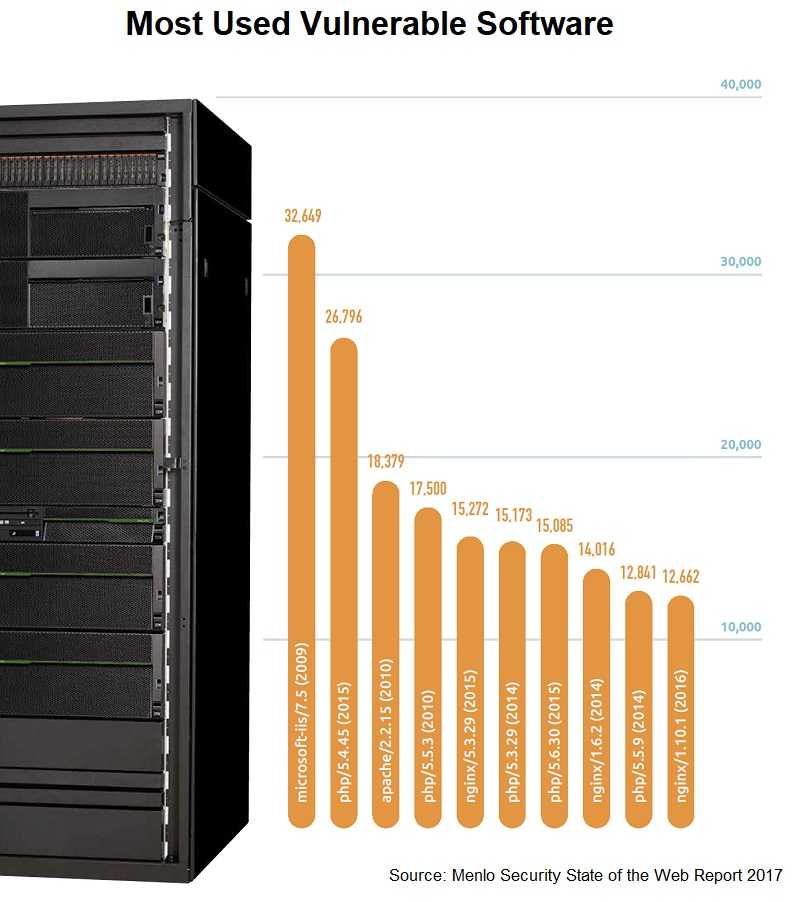
Everyone likes to be a winner. However, when the prize is being a cybercriminal’s attack vector of choice, there probably will not be a big celebration with a trophy ceremony and shaking of the president’s hand. But, that’s what Microsoft is facing, according to a report from Menlo Security. And if that isn’t enough, the report found that Microsoft will also be most exploited for its vulnerabilities into the future.
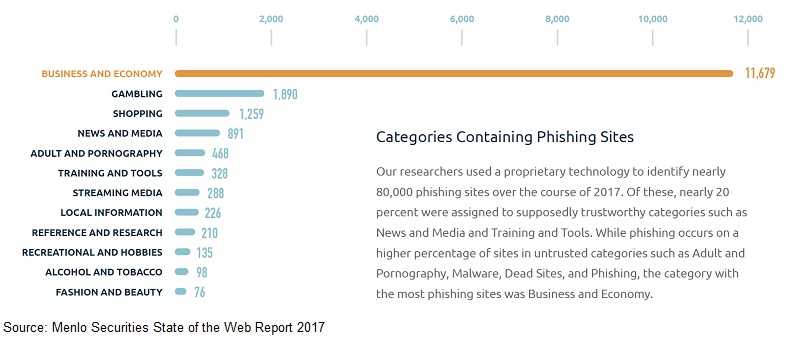
Typosquatting or Do-jacking is alive and well. Cybercriminals purchase domains that are a typo away from a popular site in the hopes that people will unwitting land on their phishing site which by the way, looks identical to the real site. Once a person is on the site, many things could happen with the worst being malware that takes advantage of a software vulnerability on their computer. The site could also attempt to get login credentials and that could go very bad quickly. Any time a hacker can log into an account, someone is in for a very bad day.
The report goes into some technical detail of specific logged vulnerabilities and even discusses the latest Microsoft Word vulnerability that also uses Adobe Flash to deliver malware. But what is important to note is that all of these listed ones arrive in someone’s email inbox as attachments.
 Phishing is not going by the wayside any time soon. That’s because it takes advantage of human nature. For the most part, humans are curious creatures. They want to know what’s behind Door Number 1. So, they click links and attachments, sometimes not being completely certain they are safe. Humans are also trusting and if they see an attachment or link in email from a colleague or vendor, they will not always use caution before clicking. And Google reported a while ago that far more email lands in the email inboxes at work than at home, which means those clicks can really put your business at risk.
Phishing is not going by the wayside any time soon. That’s because it takes advantage of human nature. For the most part, humans are curious creatures. They want to know what’s behind Door Number 1. So, they click links and attachments, sometimes not being completely certain they are safe. Humans are also trusting and if they see an attachment or link in email from a colleague or vendor, they will not always use caution before clicking. And Google reported a while ago that far more email lands in the email inboxes at work than at home, which means those clicks can really put your business at risk.
Everyone should use caution; that includes executives and board members. This rule and the risk isn’t limited to any single person or group. The report notes that email is the most prevalent form of communication in business these days and that a carefully crafted email message, in the right context, “can convince even the most security-conscious user to open an email from an unknown source, click on dangerous links, and download infected attachments.” That’s because context can evoke emotional response as well as pique curiosity of humans. Attackers know this. And they know that if it appears to be from someone the recipient knows, or is familiar with, they are more likely to click.
Always be sure before doing that. If you are not expecting it, don’t just click away. Verify it first and make sure it’s safe. Just by slowing down a little bit to do this, you can save your organization a lot of grief.