It’s Baaack! Dorkbot Banking Trojan Makes a Comeback
By: Jim Stickley and Tina Davis
September 10, 2018
The banking Trojan that fell off the grid for six years is back with a vengeance. Dorkbot has reemerged after its debut in 2012 to capture the #2 spot in banking malware. A recent Check Point trends report finds the malware is back and “better” than ever. Dorkbot successfully stole sensitive banking information from over one million devices globally. With good reason, Dorkbot is once again a source of concern among cybersecurity experts.
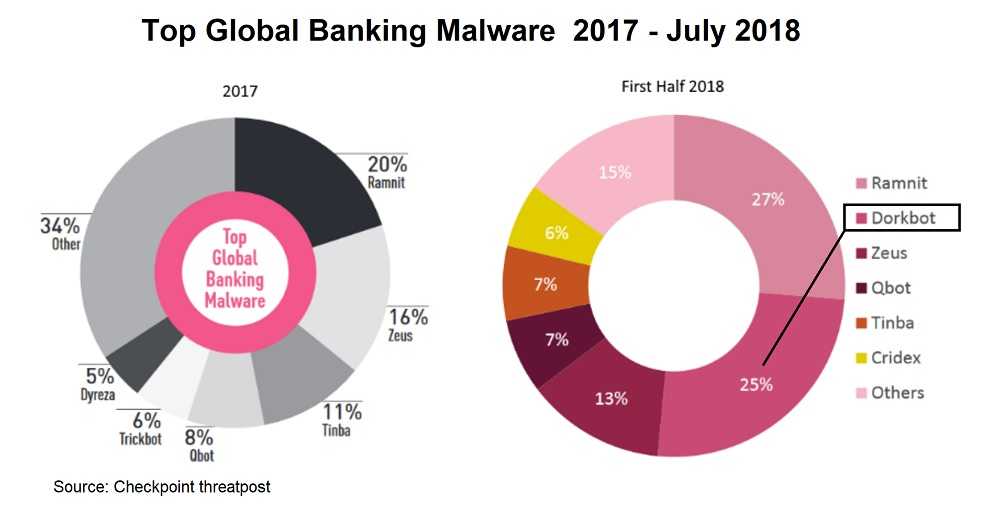
Check Point observed Dorkbot’s resurrection from their 2017 to 2018 trends report. In 2017, the report showed the top three global malware banking threats as Ramnit at 20%, Zeus at 16% and Tinba at 11%. Incredibly, Dorkbot wasn’t even on the radar. In just one year, Ramnit is still in first place currently at 27%, with the forgotten Dorkbot now taking second place, amazingly just 2% behind first place. Zeus dropped into third at 13%. Dorkbot may have slipped into obscurity over the past six years, but this recent report shows Dorkbot may have been gone, but hackers improving the malware have made sure it’s not forgotten.
Malware is known to improve with age and hacking trends, and Dorkbot is no different. Evolving over time, Dorkbot now steals login credentials from users as they access their banking websites. According to Check Point, Dorkbot now uses web-injects that activate with logins. In the financial realm, web-injects intercept data being sent from the user to their financial institutions, allowing that sensitive information to be stolen. Hackers then use your banking information, including passwords and credit card numbers, to have a financial payday on your dime. Catching Dorkbot before it wreaks havoc is currently not possible. It uses an injection technique called “Early Bird” that avoids detection by security software. It also spreads its malware by targeting the contacts of its victims, then the contacts of their contacts and so on. Both malicious and infuriating – they don’t call it “malware” for nothing.
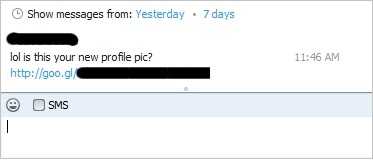 Dorkbot’s original debut took hold by conning Facebook, Twitter, and Skype users to download a malicious .zip attachment titled “Lol is this your new profile pic?” Over one million users and their devices were unaware of how a simple look at their profile picture could do so much damage. Six years ago, unsuspecting consumers were more likely to fall for an irresistible taunt about a profile pic, no matter whom the sender was.
Dorkbot’s original debut took hold by conning Facebook, Twitter, and Skype users to download a malicious .zip attachment titled “Lol is this your new profile pic?” Over one million users and their devices were unaware of how a simple look at their profile picture could do so much damage. Six years ago, unsuspecting consumers were more likely to fall for an irresistible taunt about a profile pic, no matter whom the sender was.
 Today, however, everyday users need to be much more informed and on the lookout, than they used to be. We know hackers of all types rely on human emotion as a proven method for success and they’re only too happy to exploit it. Informed users are aware of the perils of opening emails or clicking on attachments from suspicious or unknown senders – at home and at work, no matter how strong the tug on their emotions and curiosity may be. We now know hacking tactics evolve over time and Dorkbot’s newfound success is proof of that. Keeping aware and up-to-date on how to avoid hacking pitfalls is now a responsibility for us all.
Today, however, everyday users need to be much more informed and on the lookout, than they used to be. We know hackers of all types rely on human emotion as a proven method for success and they’re only too happy to exploit it. Informed users are aware of the perils of opening emails or clicking on attachments from suspicious or unknown senders – at home and at work, no matter how strong the tug on their emotions and curiosity may be. We now know hacking tactics evolve over time and Dorkbot’s newfound success is proof of that. Keeping aware and up-to-date on how to avoid hacking pitfalls is now a responsibility for us all.