The Vulnerabilities That Exchange Your Servers For Hacker Access To Your Network
By: Jim Stickley and Tina Davis
March 16, 2021
UPDATE: Microsoft released a one-click mitigation tool for those that have yet to patch their Exchange server vulnerability that is being actively exploited.
The first week of March, the European Banking Authority became a victim of cyberattack, blamed on the hacking group, Hafnium. Security experts believe the group has been breaking into companies, large and small, through the Microsoft Exchange servers. According to cybersecurity company, Volexity, the attackers likely exploited an unpatched vulnerability. Working with Volexity, Microsoft issued an emergency patch on March 2 to plug it. Unfortunately, because companies have been slow to apply it, Check Point researchers have said their researchers saw a doubling in attacks within a 24-hour period and that doubling keeps on going.
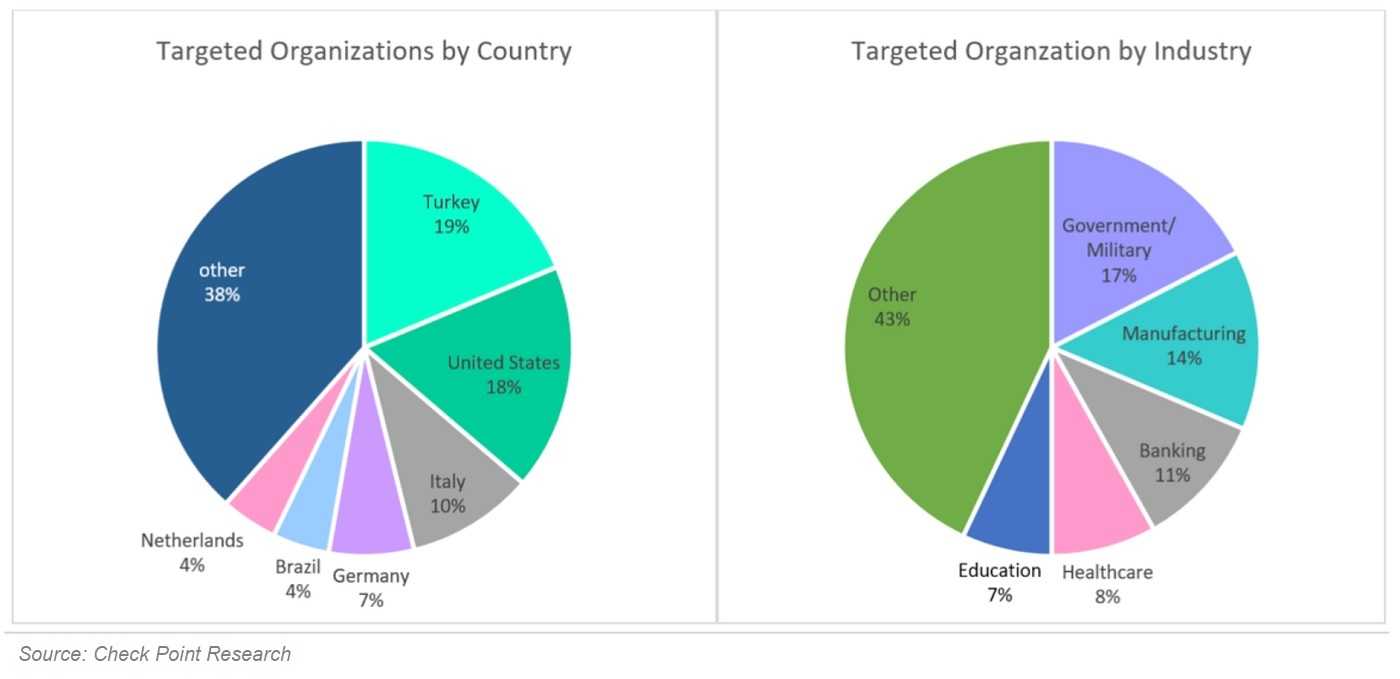
The bad news just keeps coming too. Palo Alto Networks estimates that at least 125,000 servers are still left unpatched and ESET has said that no less than 10 APT (Advanced Persistent Threat) groups are currently taking advantage of unpatched Exchange servers. This week, Microsoft said that ransomware, identified as DearCry is also using the vulnerabilities in attacks and compares it to 2017s WannaCry incident that paralyzed companies worldwide. The current industries most impacted are Government, military, manufacturing, and financial services. The hardest hit countries are Turkey (19%), the United States (18%), and Italy (10%). The vulnerabilities, noted as critical are CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065 and impact the following:
- Exchange Server 2013

- Exchange Server 2016
- Exchange Server 2019
What damage can be done? Well, a compromised server may enable an unauthorized attacker to steal your corporate emails and let loose malicious code inside the organization, with escalated privileges. Organizations that have not yet taken measures to patch these vulnerabilities should take a moment now to do that. While you’re at it, scan your network for live threats and deal with them immediately.
Remember that if you find malware in your network at any point, it doesn’t just go away once you apply patches. You have to take steps to get it out. If you cannot take care of that internally, be sure to hire an organization that has experience doing this to help.