Zerologin Exploit Requires Zero Credentials To Become Your Administrator
By: Jim Stickley and Tina Davis
December 29, 2020
If you are in charge of patching Windows server systems for the U.S. federal government, you should have received notification about an emergency directive that needed your immediate attention. And that notification came over the weekend of September 19 with a deadline of September 21, 2020 to apply a particular patch. If you’re in charge of patching those systems for any other type of organization, you should get right on it too, because the vulnerability the patch addresses has just become even more of a risk.
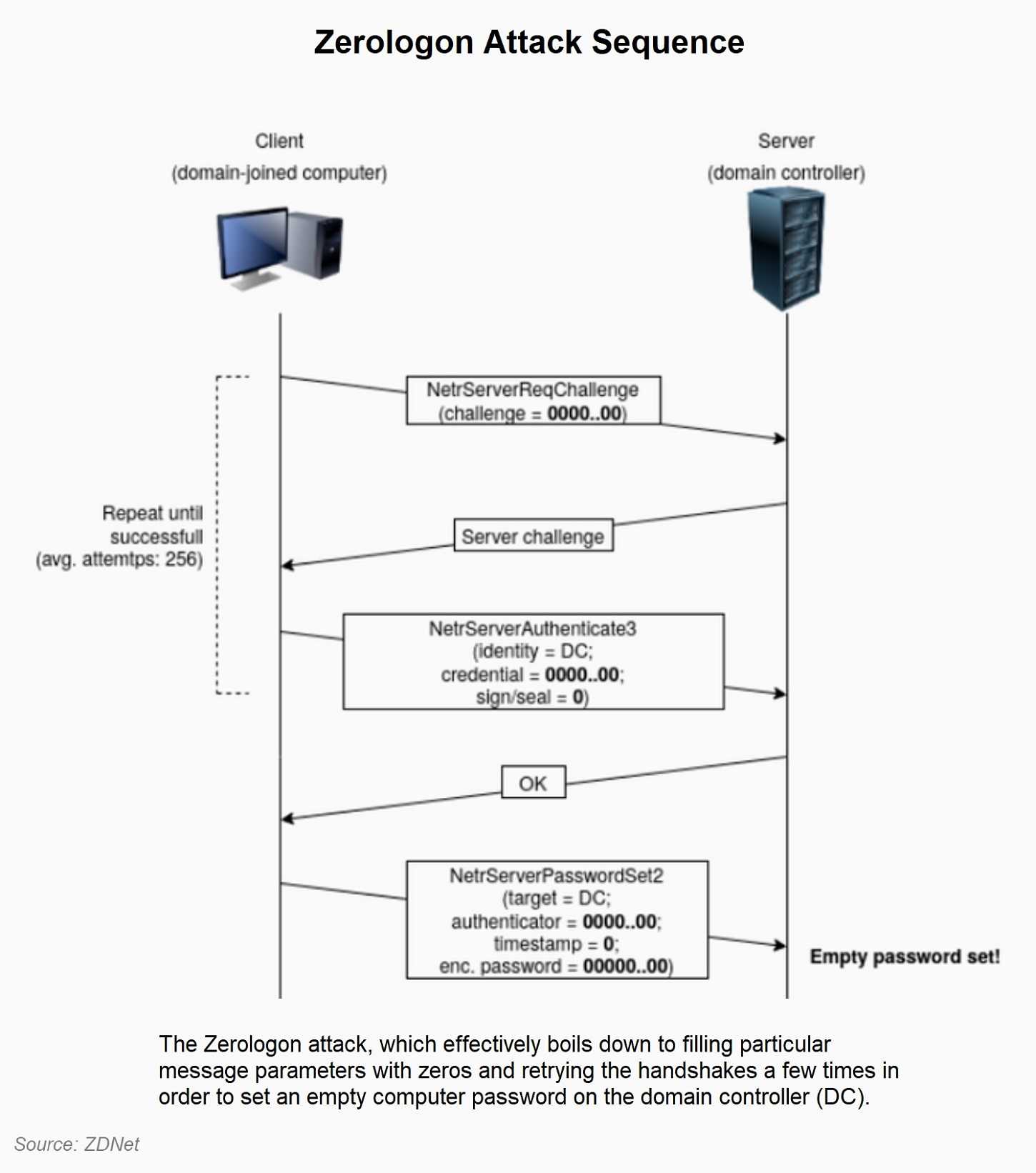
Emergency directive 20-04 required all federal agencies to take immediate action regarding the Zerologon exploit. The vulnerability that Zerologon takes advantage of was actually uncovered a while back and a patch was released in August to fix it. But what is making it more of a cyber threat now is that code that demonstrates just how to make the exploit succeed was recently released into the public domain for anyone who desires to try it. If Zerologon is unleased at your organization, it can allow an attacker to gain elevated privileges to the unpatched server and become an instant administrator. It doesn’t even require the attacker to get logon credentials.
Ok, so in this case login information is not needed, but applying the patch posthaste is definitely needed. It’s still important, especially if you are an administrator, to have strong credentials. It’s also important to allow access to various areas of any organization to only those who need it. You see, the more access a person has to information, the more risk one poses to the entire organization. So, limit access to only what someone needs to have in order to effectively do the job.
When a developer or vendor issues a patch or update to any product, it’s particularly important to jump right on getting it applied. This is even more true if the fix is repairing a critical or high severity issue, as this one is. According to reports, it’s expected that this code will be weaponized very quickly. To look up more details, check out CVE-2020-1472.