Is Timing Everything? Major Instagram Flaw We're Just Hearing About Now
By: Jim Stickley and Tina Davis
February 10, 2021
No one wants to think any app platform would sit on a massive security flaw in its software and not go public with it right away. And what happens when that app is the hugely popular Instagram and the flaw allows remote takeover of an Android mobile device? Instagram, a wildly popular app owned by those at Facebook, has nearly one billion users daily who upload over 100 million photos every day. Facebook, no stranger to very public security flaws, says it provided a patch for the Instagram bug in the middle of 2020. The fix has been shrouded in secrecy for reasons known only to Facebook and was just recently disclosed publicly.
Researchers at Check Point discovered the critical vulnerability and notified Facebook immediately. The flaw, tracked as CVE-2020-1895, allowed remote attackers to overtake a device and turn it into a spying tool that gained full access to a victim’s Instagram account. The PII (personally identifiable information) compromised included private messages, the ability to post and delete photos, device storage, contacts, and location data. If you’re interested in knowing the extent of what Instagram collects about you, visit the official webpage, and click “Data Policy.” Spoiler alert: It’s a ton of data.
Surprisingly easy to pull-off, all an attacker needed to do was send a malicious image to a target’s email or Instagram account. Once the image is saved and opened in Instagram, the exploitation began – all with the account holder being none-the-wiser. It’s believed malicious code was embedded in the images; a technique known as steganography. No matter what you call it, the damage already done to mobile Instagram users who didn’t download the security patch months ago could be massive and possibly irreparable.
Knowing now about the Instagram vulnerability and how easily it worked should be a reminder to us all not to take app security for granted. Implementing security basics is not difficult and the following tips should be followed whenever downloading and using an app. Blind trust could have consequences and may take some time before an app’s flaws become known.
App Security Basics
 Apply app security patches as soon as they are available. As we know, waiting to do so may have devastating results.
Apply app security patches as soon as they are available. As we know, waiting to do so may have devastating results.
- Read reviews of an app before downloading it. Other’s comments and findings can provide a warning about the negative attributes an app may have.
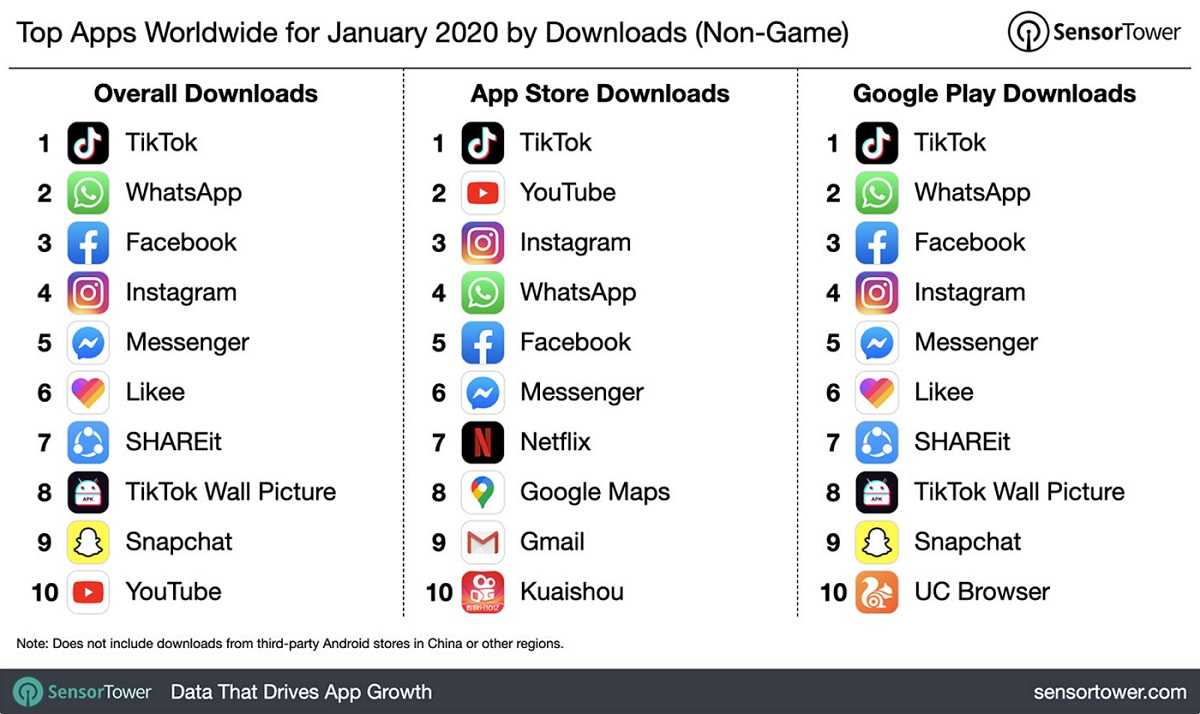
- Always download apps from the official Google and Apple app stores, or the official store for your particular device. Going to a third-party site for apps (sideloading) is very risky since they don’t always scan for malware before making them available. Although not always perfect, the official app stores make scanning for malware a priority before releasing an app.
- Pay attention to app permission requests when downloading. Although they pop-up quickly, many user’s hit “allow” without reading what exactly they are giving the app access to. Take time to read them and use common sense to guide your response. For example, would a gaming app really need to access your contacts or photos? Common sense should always be part of having app cyber-smarts.