Global Voicemail Scam Targets Enterprise Email; Mimics PBX System
By: Jim Stickley and Tina Davis
July 22, 2020
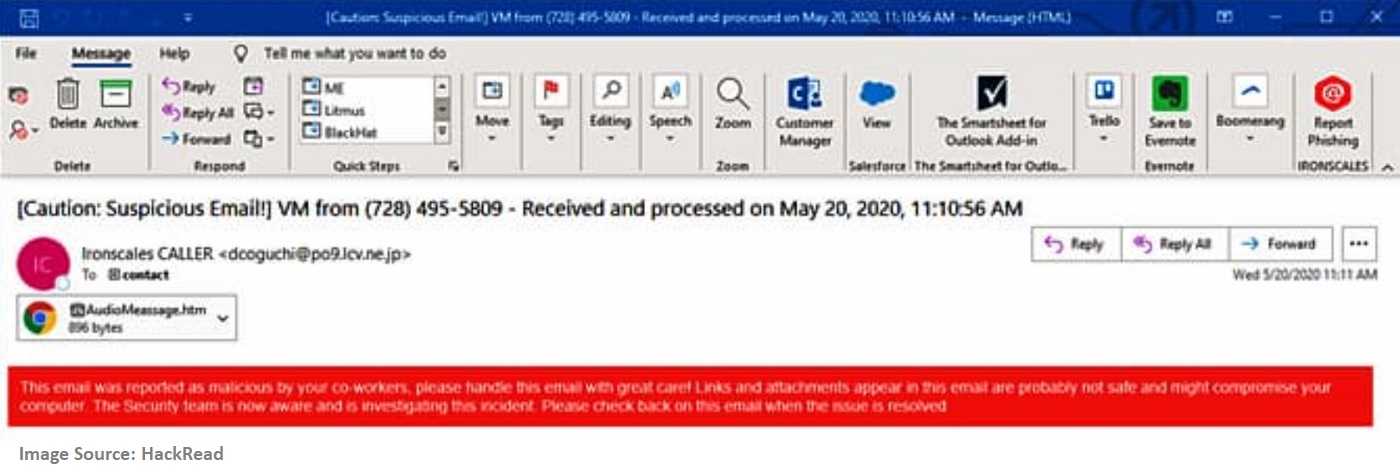
A massive, global voicemail phishing scam was recently exposed and known to affect at least 100,000 email inboxes worldwide. IRONSCALES Security discovered this scam targets healthcare, real estate, IT, financial, and other enterprise with a spoofed (fake) voicemail to email translation. These emails appear to be from PBX (Private Branch Exchange) phone systems used at offices, and they are very targeted. PBX telephone networks are used by enterprise for internal voice calls within a company, and for external calls to and from clients, vendors, and other outside contacts. Unfortunately, many employees are getting caught up in this socially engineered and highly effective vishing campaign.
Employees using a PBX system to translate voicemails directly into email accounts are the targets for this vishing scam. These attacks are considered socially engineered, which are highly targeted to the recipient. They use personalized subject lines, appear to be from work and also use the recipient’s name, company name, and other coworker names. Doing so adds credibility to the illusion that they are legitimate and therefore safe. This scam is particularly effective at a time when more employees than ever are working from home and still need to navigate business related calls to their office voicemail. Many are using voicemail to email translation and that’s when this vishing scam gets to work.
Keeping work details like company name, position, and names of employees from sites like LinkedIn and Facebook is always recommended by security professionals. Hackers like to troll company websites to get the employee PII (personally identifiable information) necessary to feed their socially engineered attacks. Sharing enterprise PII on public websites is what bad actors are looking for to successfully pull-off this vishing scheme. Having a low profile online can help limit how effective these scams can be. Being as generic as possible on these sites, as well as on all social media sites can help prevent attacks like this.
Using anti-phishing awareness also helps ferret out phishy emails before they are acted upon. A healthy dose of suspicion goes a long way protecting recipients from email phishing scams. Generic greetings, bad spelling and grammar, subject lines that look to invoke a quick response using scare tactics, tugs on heart strings, and demands for immediate attention are automatically phishy. Any email that requires providing login details, account information like passwords or payment information, are also big phishing red flags. Remember, if an email doesn’t pass any of the phishing smell tests, it’s always safer to delete it than to be sorry you didn’t.