U.S. Postal Service Delivers Email Phishing Campaign
By: Jim Stickley and Tina Davis
February 4, 2020
An international ransomware attack targeting Germany and Italy has landed on U.S. shores. Proofpoint discovered a blitz of phishing emails claiming to be from the United States Postal Service (USPS). It observed thousands of phishing emails with malicious Microsoft Word attachments containing the IcedID banking Trojan. The email phishing campaign impersonated the USPS as the messenger for the malware attachments, hoping to capture victims using the legitimacy of the organization as bait.
Discovered in 2017, IcedID Trojan targeted financial institutions to steal user credentials, including customers of payment card providers and banks. This particular discovery is aimed mostly at the healthcare industry, another immensely popular target for ransomware.
Using the domain “uspsdelivery-service.com” to deliver the Microsoft Word attachments, the email text contains a message that the recipient needs to open and read the attachment to avoid tax-related issues. Instead, the Word document installs the IcedID Trojan. In a 2018 discovery, Proofpoint found another phishing campaign in the U.S. using the IRS as the email sender, also with a tax-related lure in the text.
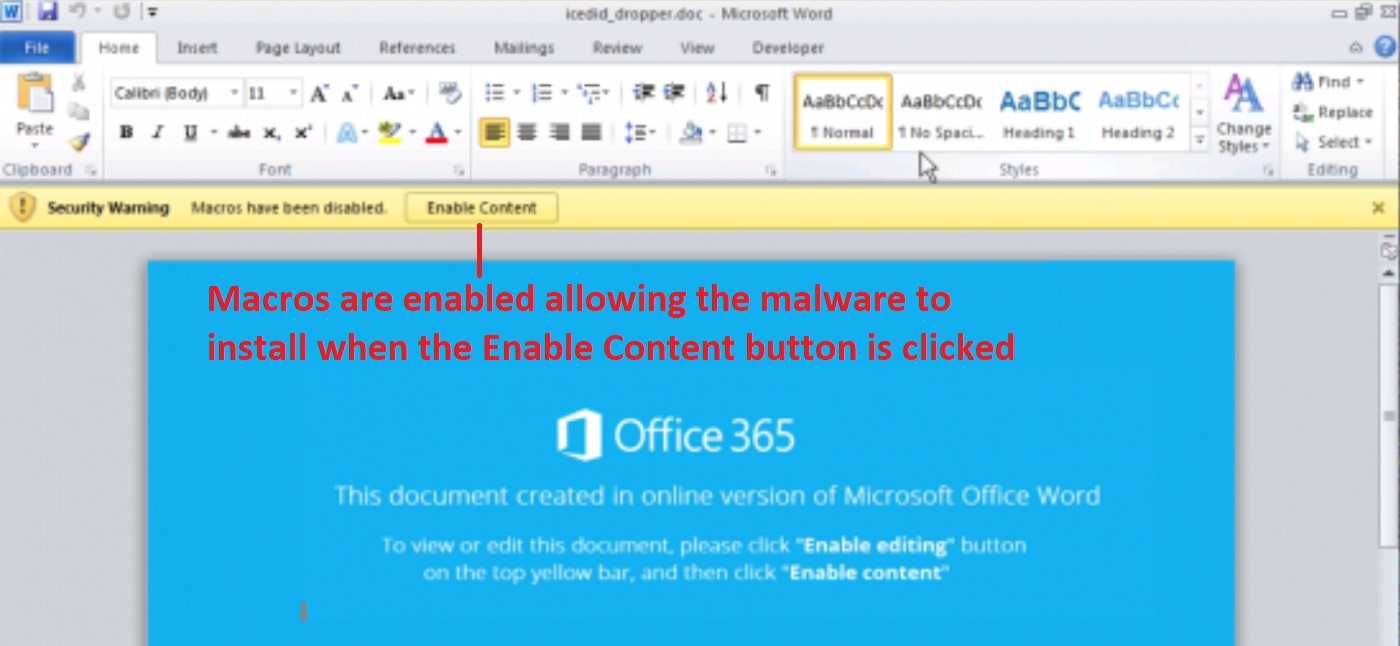
Posing as legitimate senders from reputable organizations is a cybercriminal favorite. They often trick recipients into opening attachments or clicking on a link, and both can install malware on a device. Other phishing campaigns were previously discovered using Maze and Cobalt Strike to execute ransomware attacks, with the most recent using IcedID for malware delivery. Proofpoint believes a new hacking group has taken the reins and now is behind the IcedID campaign.
 Like many cyberattacks, keeping ahead of email phishing campaigns takes some attention to detail. Since hackers take advantage of using legitimate organizations, it’s not always easy to tell the real from the fabricated. One tactic many phishing emails rely on is using a sense of urgency in the subject line. No subject is off limits as long as it motivates recipients to open the email and act on attachments or links in the text, or provide log-in and other credentials. Certain employees are more vulnerable to attacks, especially those who work in positions dealing with finances and other sensitive matters, as well as those in high level positions.
Like many cyberattacks, keeping ahead of email phishing campaigns takes some attention to detail. Since hackers take advantage of using legitimate organizations, it’s not always easy to tell the real from the fabricated. One tactic many phishing emails rely on is using a sense of urgency in the subject line. No subject is off limits as long as it motivates recipients to open the email and act on attachments or links in the text, or provide log-in and other credentials. Certain employees are more vulnerable to attacks, especially those who work in positions dealing with finances and other sensitive matters, as well as those in high level positions.
Companies who view their organization from an attacker’s perspective are ahead of the game when they also focus cyber education on an employee’s particular job function. Emails claiming to be from legitimate senders can be easily verified and should always be checked. Going directly to the official website the email claims to be from is a great way to find out if the sender is legitimate. If it’s for real, the website will have a record of what data it’s asking you to provide, open or click. Always remember, verify first and act second.