Know The Signs: A Ransomware Attack Is Closer Than You Think
By: Jim Stickley and Tina Davis
May 8, 2021
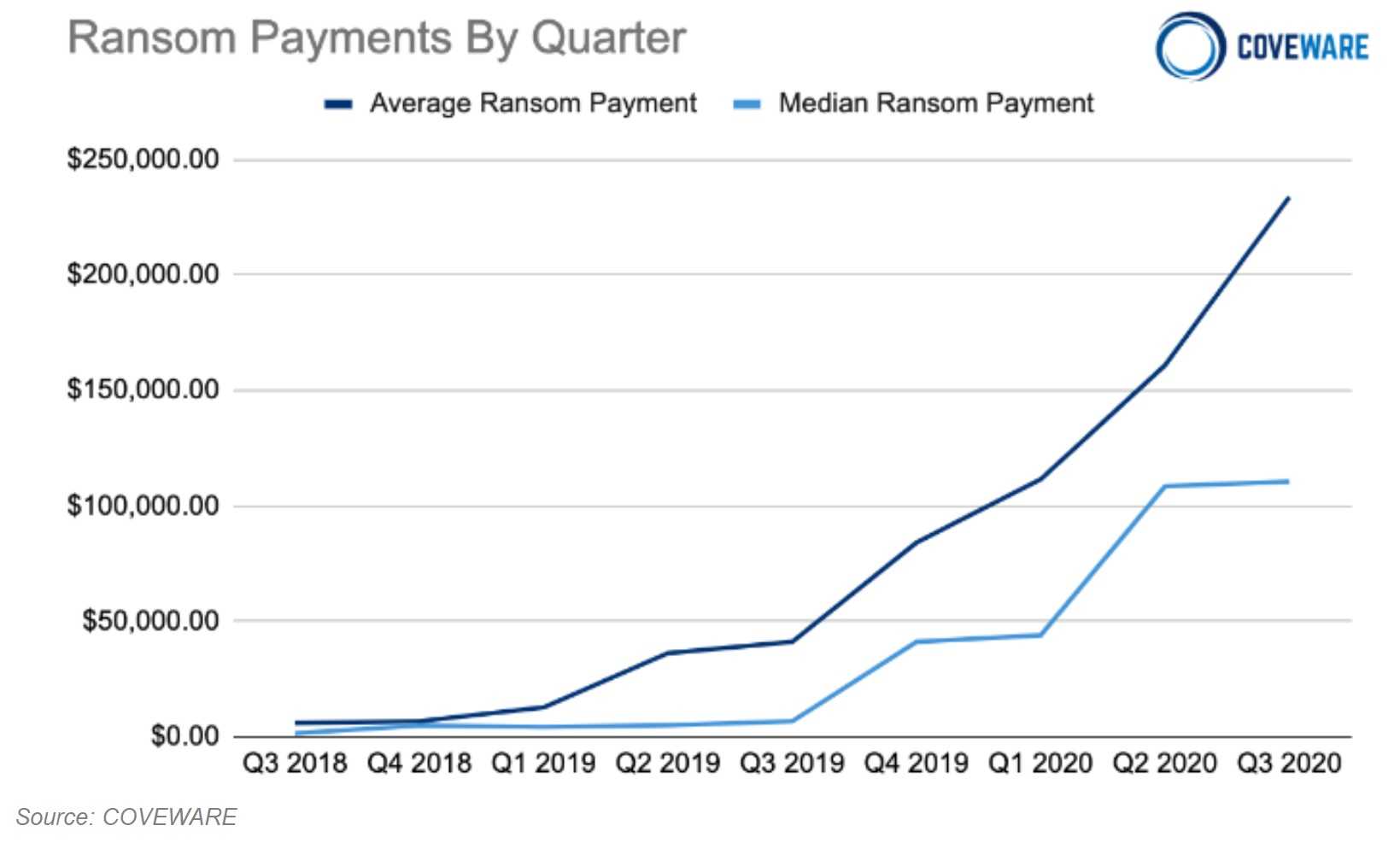
Ransomware attacks have crippled countless organizations in many sectors including commercial, finances, healthcare, government services, and education. They’ve proven devastating and expensive to fix, with some organizations never recovering and having to permanently close their doors. When ransomware strikes, all network data is encrypted and impossible to access. Unprepared victims are left with the only alternative to pay a ransom demand to return their hijacked data. According to a Coveware report, the average ransom payment at the end of 2019 was $84,116, over twice the ransom amount of attacks earlier that same year.
Cyber history tells us that an organization has from 48 hours to 12 days to act before a ransomware attack takes over data systems. However, experts find these attacks leave traces that they are about to strike. Cybersecurity experts share the signs that ransomware has entered a data system, hoping the attack can be mitigated before it’s too late. Part of that mitigation should first include preventive measures like evaluating your overall data security and how safe your business systems appear to a potential attacker.
BOLO: Ransomware Attack Red Flags
 Multiple Login Failures. If there are three or more login failures in a row on an administrator account, it’s a very likely sign a network has been attacked. Closely monitoring failed administrative and RDP (remote desktop protocols) logins let you know a full ransomware attack isn’t far behind.
Multiple Login Failures. If there are three or more login failures in a row on an administrator account, it’s a very likely sign a network has been attacked. Closely monitoring failed administrative and RDP (remote desktop protocols) logins let you know a full ransomware attack isn’t far behind.
- Brute-Force Attacks on RDP Systems. These attacks systematically flood accounts with passwords until a match is found. Also, watch for unexpected file-copying as it could mean attackers have breached administrative accounts and have started copying network files. Ransomware can also use those compromised administrative accounts to rapidly enter and encrypt file systems.
- Multiple Questions About a Single Device. When the network receives questions about a device like “What is the domain and company name?” or “Is this a Mac or Windows device?” it’s time to investigate further. That’s because attackers will also attempt to find out what else is part of the network and how it can be accessed.
- Phishing Emails with Unfamiliar Domains. If these emails start arriving with strange domain names unknown to a company, analysis tools can help filter trusted domains from potentially bad domains. Analysis tools can also look at download histories and find those that are questionable.
- Security Tools Used to Disable Security Software. With administrative rights in the hands of an attacker, they can disable security tools and forcibly remove software security applications. Although these removal tools are legitimate, should they start showing up on an unassigned system, it’s another sign that further trouble is on its way.
- Network Traffic Redirected to Dark Web Locations. Odd DNS (domain name system) requests, including those leading to questionable dark web locations and known malware sites are signs that a network could be infected and further compromised.
Don’t forget to do regular backups of important system data and keep it separated from the operations and production networks. This will allow rapid restores should ransomware strikes. Paying a ransom is something the FBI strictly warns not to do as it only encourages further attacks.