Revised Banking Trojan Spams 75,000 Users
By: Jim Stickley and Tina Davis
September 25, 2017
Maybe you don’t care about the names of all the various versions of malware out there. In fact, it probably just confuses you more. In all honesty, there is no reason to remember them all or even distinguish them from each other for most people. So when you read that the TrickBot banking Trojan is wreaking havoc again, you can just skip to the next section for tips for ensuring that it or any other malware doesn't land on your mobile device and steal your online banking credentials.
Regardless of what type of malware you may get infected with, it almost always gets on your devices through some kind of phishing. So keep these avoidance tips in mind:
 If you receive an email message, text message, or chat message from someone you don’t know and it includes any attachment or link, consider it suspicious and don’t click on anything.
If you receive an email message, text message, or chat message from someone you don’t know and it includes any attachment or link, consider it suspicious and don’t click on anything.
- If a message arrives from someone you do know, whether colleague, acquaintance, friend, or family member and inside is a link or attachment that you are not expecting to receive, consider it suspicious and don’t click on it immediately.
- If you are not quite sure if links or attachments are legitimate, contact the sender separately from the email or text and verify it before taking any action. In other words, don’t directly reply to the note.
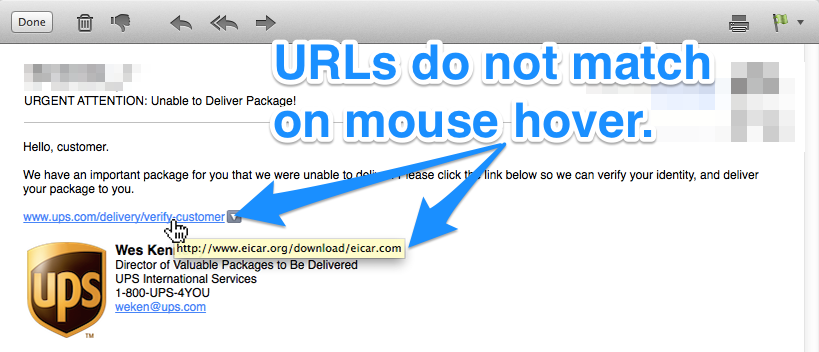
- Even if you are quite certain a link is legitimate, hover over it with your mouse pointer first to see if it’s headed to a site you expect. Many phishing links are truncated on mobile devices, but you can hold down on the link for several seconds to see the entire link before quickly depressing it to get to the site. Just be careful to hold down long enough.
- Always keep anti-malware software on all devices and keep them updated as well.
- Keep all software and applications on all devices updated with the latest versions and patches.
- If you install new hardware on your network, immediately go to the manufacturer’s website to find out if there are any updates to its software. Often these products sit on store shelves for a while and in the meantime, updates are released. Those need to be applied right away, so that if there are vulnerabilities, they are fixed right away.
 If any attachment requests that macros be enabled, as this one does, it very well could be aiming to do something malicious. Most of the time, unless you created or frequently work with a specific document that needs macros, it isn’t necessary to enable them.
If any attachment requests that macros be enabled, as this one does, it very well could be aiming to do something malicious. Most of the time, unless you created or frequently work with a specific document that needs macros, it isn’t necessary to enable them.
- Watch for typos and grammatical mistakes in email messages that you are not expecting. If they come from a company, they should look and sound professional. And although even the most official documents can still have errors, they should be suspect until you can rule out any foul play.
- Any time you get a note that something in any of your online accounts needs to be verified, updated, or changed, go into your account directly from the website. There is no need to click links in messages to perform those functions, even if the request is valid.
And in case you do want more information on the latest outbreak of TrickBot, researchers at Cyran found that a spam campaign sent out over 75,000 email messages in 25 minutes. They all claimed to be from one of the UK’s largest banks, Lloyd’s Bank. As is common with these types of Trojans, some attached documents needed review and signatures. The subject was “Incoming BACs,” which is a reference to a system that allows users to make payment from one email account to another. If the attachment is clicked, it redirects to a site that is identical to the real one of Lloyd’s Bank, proving just how sophisticated these phishing campaigns have become. It even uses the genuine digital certificate and URL. The only giveaway is the email address from where the phishing message is sent. Rather than using the correct Lloyd’s Bank domain of lloydsbankuk.co.uk, it is from the incorrect lloydsbacs.co.uk.
In this case, TrickBot targeted UK users, but it has been seen en masse in the U.S. and Australia as well. It’s just modified to be relevant to those countries.