Hackers For Hire Spice It Up And Offer Espionage Services
By: Jim Stickley and Tina Davis
March 3, 2022
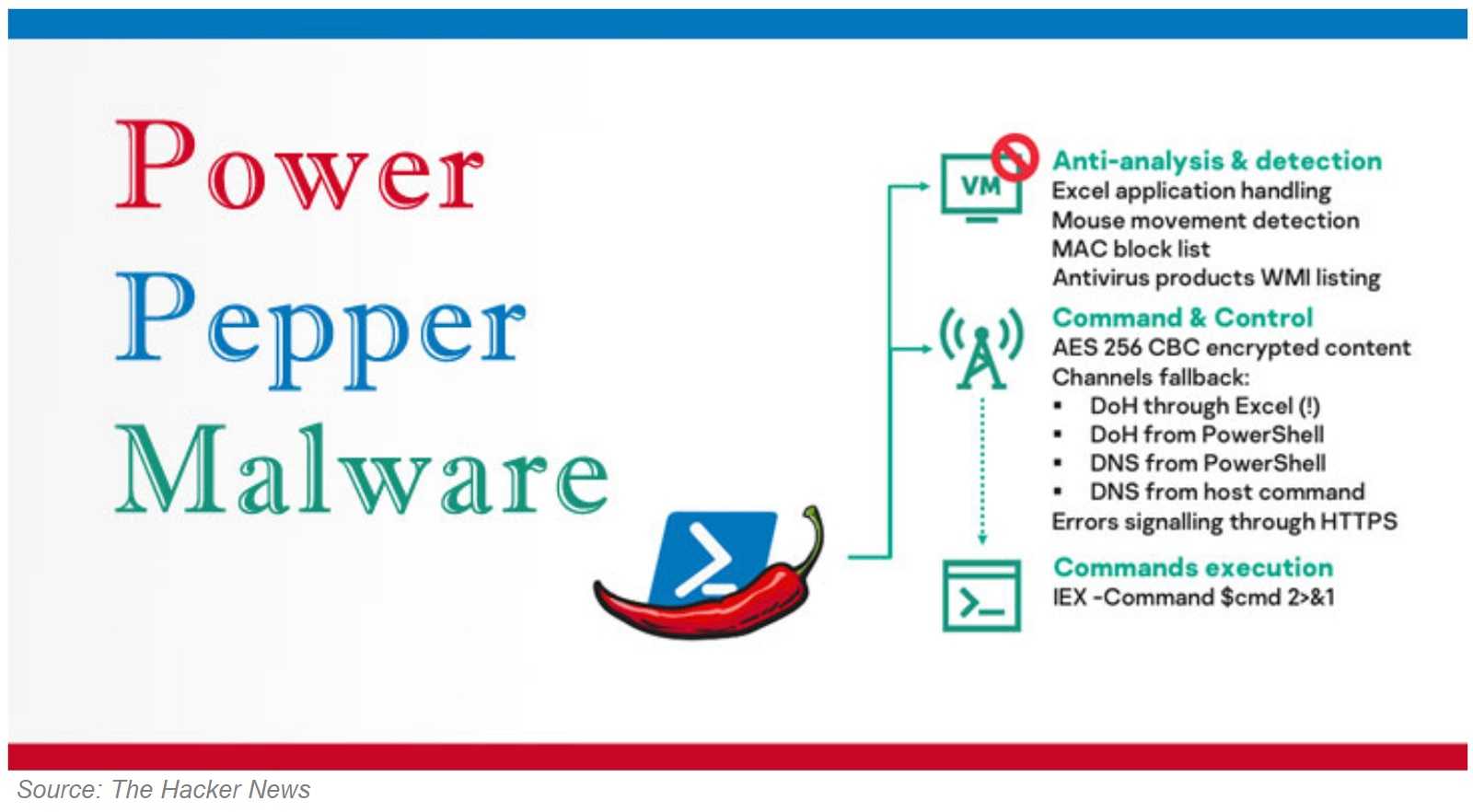
If the name of the hacking group DeathStalker doesn’t grab your attention, what they do will. They’re a mercenary group of hackers-for-hire and they offer their espionage services to the highest bidder. They also have a history of targeting the legal and financial sectors. Kaspersky discovered DeathStalker in 2018, although the group goes back to 2012. They’re an APT (advanced persistent threat) group offering their spying techniques for hire. In November, Kaspersky noted the group had a new malware weapon to work with and it has new ways to hideout on a data system and spy. It’s dubbed PowerPepper by researchers, and it’s a backdoor threat that successfully hides behind a victim’s file traffic and looks just like another file.
Adding to its evasion techniques, PowerPepper uses steganography as part of its stealthy plan. Steganography is the practice of hiding data in images--and that data is likely malicious in nature. PowerPepper sends emails with innocent-looking pictures of peppers or ferns. The pictures are full of the new malicious code that evades antivirus software, including at startup. When that happens, little to nothing can stop PowerPepper from going forward with its spying gig.
DeathStalker uses spear phishing emails to jumpstart PowerPepper’s system infiltration. Spear phishing emails target a specific individual, often by name, and appear to be from a trusted source. Kaspersky finds PowerPepper embedded in spear phishing emails that use a malicious link in the content, or in an attachment hiding as a Word or ZIP document. Since spear phishing emails are the preferred method of delivery for this snooping malware, reviewing how to spot the red flags of email spear phishing and how to avoid them is wise.
Find and Avoid Spear Phishing Emails
 Just because an email uses your name and looks legitimate, it doesn’t mean it can be trusted. If it’s from someone you know, text or call them to verify before acting on it.
Just because an email uses your name and looks legitimate, it doesn’t mean it can be trusted. If it’s from someone you know, text or call them to verify before acting on it.
- Don’t click on links or open attachments in emails you’re not expecting, look suspicious or are from an unknown sender. It’s a hacker’s favorite way to deliver malware.
- Limit the amount of personal information on social media accounts and networking websites. Hacker’s troll these sites to gather details on victims, including your employer and names of your friends and family. It’s the small clues that help make spear phishing successful.
- Look for bad grammar and spelling mistakes. They’re a sure sign it wasn’t written by an English major and should be considered suspicious.
- Enable two-factor authentication (2FA) as it adds and extra layer of security to your data and identity.