It’s hard to believe that anyone would intentionally interfere with the distribution of the long awaited, life-saving coronavirus vaccine. It’s even more difficult to know that chilling thought is now a reality. IBM X-Force recently released a report finding cybercriminals are attacking the coronavirus vaccine cold chain. The cold chain stores and delivers vaccines at the level of chill needed to be effective. Our CISA (Cybersecurity and Infrastructure Security Agency) has requested that Operation Warp Speed (OWS) and others involved in the vaccine cold supply chain review the IBM X-Force report “Attackers Are Targeting the COVID-19 Vaccine Cold Chain.” The report exposes the threat to coronavirus vaccines in the U.S. and abroad, and how they’re being targeted by a global email spearphishing campaign.
May The X-Force Be With You
IBM X-Force created a task force at the start of coronavirus and is dedicated to finding cyber threats against those involved with keeping the vaccine cold chain moving forward. It focuses on organizations and individuals involved with the cold chain supply, knowing that maintaining the necessary temperature is critical to the vaccine’s efficacy.
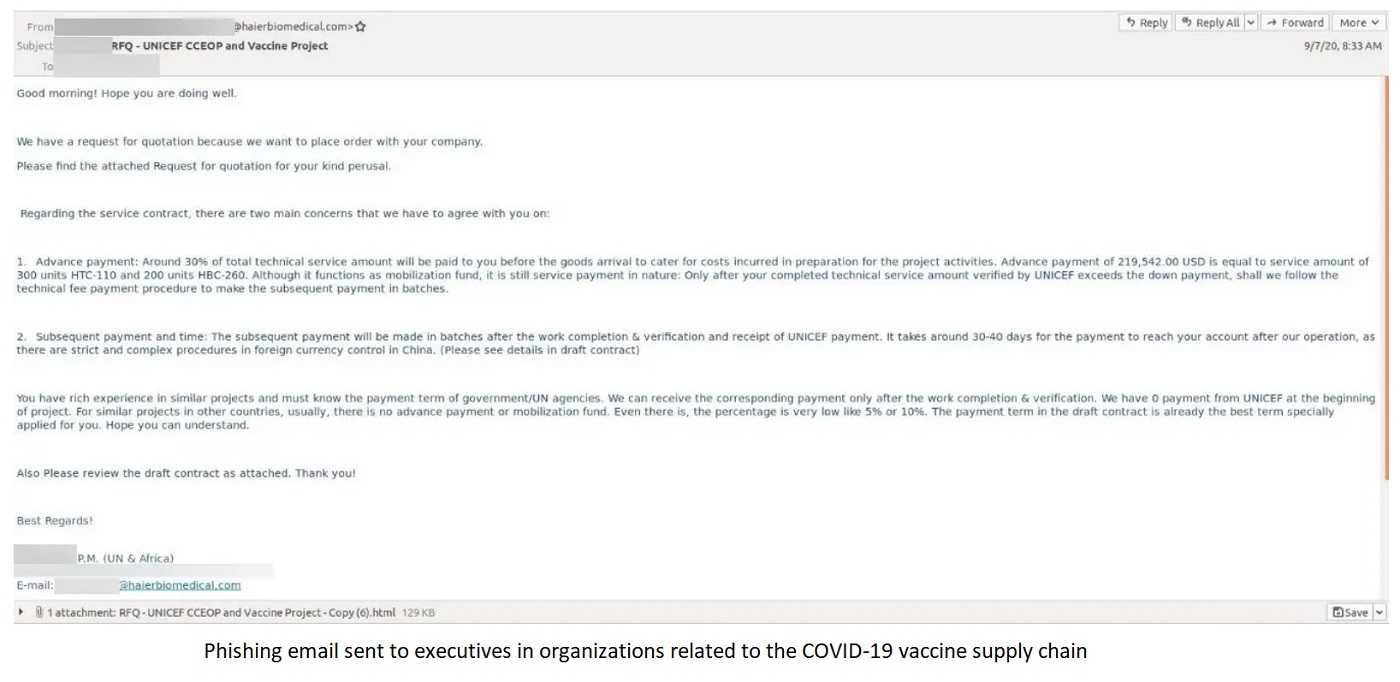
Their analysis finds the threats started in September of this year, targeting six countries and organizations in the cold chain with a widespread spearphishing campaign. The attacks prey on executives, called “whaling” since they target those at the highest levels in an organization. The attacks target “whales” in the U.S. and global organizations with laser precision, a sign that nation-state actors could be the source of the hacks. At this time, those responsible for the attacks have yet to be identified.
The Hook
Spear phishing is a specific type of email phishing that targets individuals by name and appear to be from a legitimate and trusted source. This particular attack stole the identity of a trusted executive from a well-known company that’s an integral part of the coronavirus vaccine cold supply chain. The “executive” hacker sent emails to providers who are also part of the cold supply chain. Since the spear phish sender appears to be authentic, the odds that the target will act on the email greatly increase.
High Stakes Hack
The known targets exist on a global level and any breach, large or small, could compromise the temperature and distribution of the coronavirus vaccine. It was discovered that executives involved in procurement, sales, finance, and information technology were targeted, as well as those from global organizations in greater Europe, Italy, Germany, South Korea, Taiwan, and Czech Republic. Any efforts that support the vaccine cold chain are potential victims.
One Phish, Two Phish, No Phish!
 The success of the assaults against the vaccine cold chain, or other phishing attacks in general, can be minimized or prevented by using anti-phishing cyber-smarts. Regularly educating all employees to spot the red flags and trends of email phishing attacks is a necessary step. Employees, including those at the top, are often the first line of defense against email phishing efforts. Any request for sensitive data should be verified before it’s provided. Never use the contact information, follow links, or open attachments in the email. Instead, get the legitimate contact information and use it to verify the request is legitimate before acting on it.
The success of the assaults against the vaccine cold chain, or other phishing attacks in general, can be minimized or prevented by using anti-phishing cyber-smarts. Regularly educating all employees to spot the red flags and trends of email phishing attacks is a necessary step. Employees, including those at the top, are often the first line of defense against email phishing efforts. Any request for sensitive data should be verified before it’s provided. Never use the contact information, follow links, or open attachments in the email. Instead, get the legitimate contact information and use it to verify the request is legitimate before acting on it.
Organizations also need to step-up their own cybersecurity protocols. Access to sensitive information should only be given to those who need it to do their job. Limiting access to critical data limits its exposure to attackers, whether accidental or as the result of a cyberattack. Monitoring sensitive data requests should be ongoing, and the approval of management or higher can prevent the data from ending up in the wrong hands. Considering what could be at stake, in this case with the coronavirus vaccine cold chain, it’s well worth the effort.