Credential Stuffing: Hackers Make the Most of a Data Breach
By: Jim Stickley and Tina Davis
September 17, 2019
If a data breach is big enough to make the evening news, pay attention–especially if you have an account with the breached company. Never the type to sit back after a data breach, hackers have found a new way to maximize the damage from a data theft. It’s called credential stuffing and they’re not afraid to use it. A California mother of a toddler found out security cameras in her home were overtaken by a hacker and she soon learned that as a result, her data had been “stuffed.”
 Credential stuffing is a term used to describe a specific type of hacking where user credentials are gathered by breaching a system and then used to try to break into other systems or accounts. Unfortunately, despite knowing better, very few of us use different and original login information for every account we have. This is when credential stuffing hits the jackpot. Armed with stolen personal data, a hacker uses automated programs to run all the passwords, etc. through other accounts, hoping the victim uses the same information to enter other accounts. Chances are they will access much more than the original breached account.
Credential stuffing is a term used to describe a specific type of hacking where user credentials are gathered by breaching a system and then used to try to break into other systems or accounts. Unfortunately, despite knowing better, very few of us use different and original login information for every account we have. This is when credential stuffing hits the jackpot. Armed with stolen personal data, a hacker uses automated programs to run all the passwords, etc. through other accounts, hoping the victim uses the same information to enter other accounts. Chances are they will access much more than the original breached account.
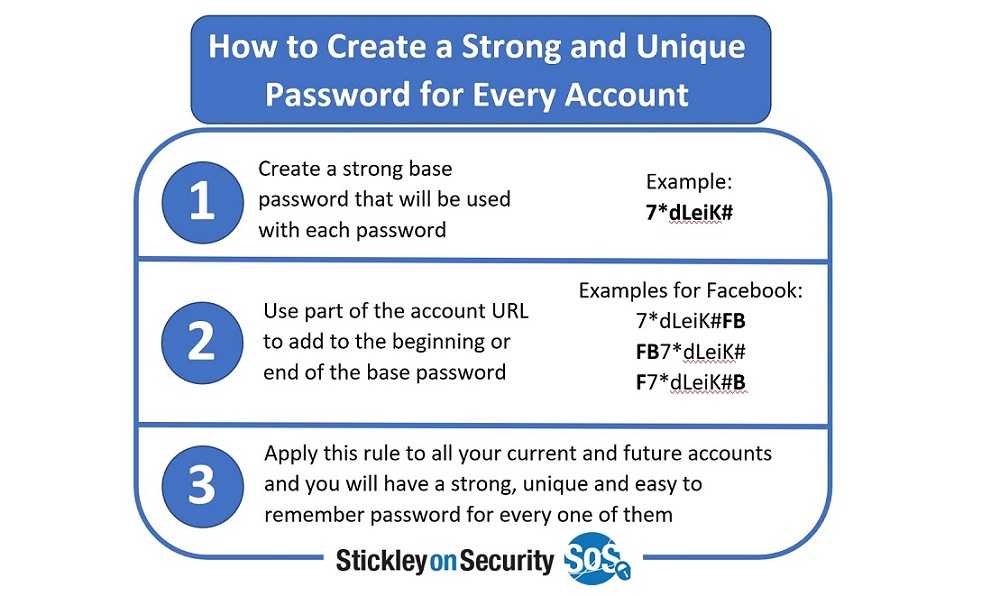
Many devices are accessible via the Internet, and that makes it easier to credential stuff. Reusing passwords and login information isn’t unusual, but when a mega breach happens, it’s a credential-palooza for those looking to capitalize by stuffing credentials. Paying attention when a mega breach occurs should be a big green light for users to change sign-in information for affected accounts. Doing so should ultimately prevent a hacker from credential-stuffing other accounts because their access has been blocked by different login data. Use strong passwords that include a combination of letters and numbers, as well a few special characters scattered throughout. In addition, always use two-factor authentication (2FA) or multi-factor authentication (MFA) when signing into accounts. It adds an additional security layer to signing in, making it nearly impossible for a hacker to gain access. This could be a text sent to your phone with a unique code that has to be entered before access is given, a randomly generated code from a keyfob, or even a list of questions with answers unique to you. There are many types of this. Just make sure to use it when it’s available.
The mother from California found out the hard way the extent of damage credential stuffing can do. Hard to believe, the security cameras in her home had been breached, but the damage didn’t stop there. Hackers then used the intercom feature to send pornographic audio into her 2-year-old’s bedroom. Once the hacker gained access to a device in her home, they credential stuffed to gain access to other home devices using the same access information.