To Pay Or Not To Pay: The Ransom Debate Continues
By: Jim Stickley and Tina Davis
October 29, 2019
The decision to pay a ransom demand or not is difficult for organizations to make. It’s a debate involving many factors, including how prepared a back-up system is to restore hijacked data, or if a backup system exists at all. Targets of ransomware may vary, but one thing for sure is hackers choose their targets carefully. The value of the data is key for hackers who believe the effect of having sensitive data locked up and inaccessible is the answer to having a ransom paid. When targets like healthcare institutions and city services are at risk, the decision about a ransom payment can have dire consequences. No matter how you look at it, the ransom debate is one that goes far beneath the surface of simply deciding whether to pay or not.
There may only be two options for a ransom demand, but an organization’s approach to cyber security factors heavily in the decision. Those without cyber-resilient systems and backed-up data may find themselves in a lose-lose situation. If the choice is made to pay-up to restore “business as usual,” there’s no guarantee the encrypted data will be unlocked by hackers, or that an even higher ransom will be demanded.
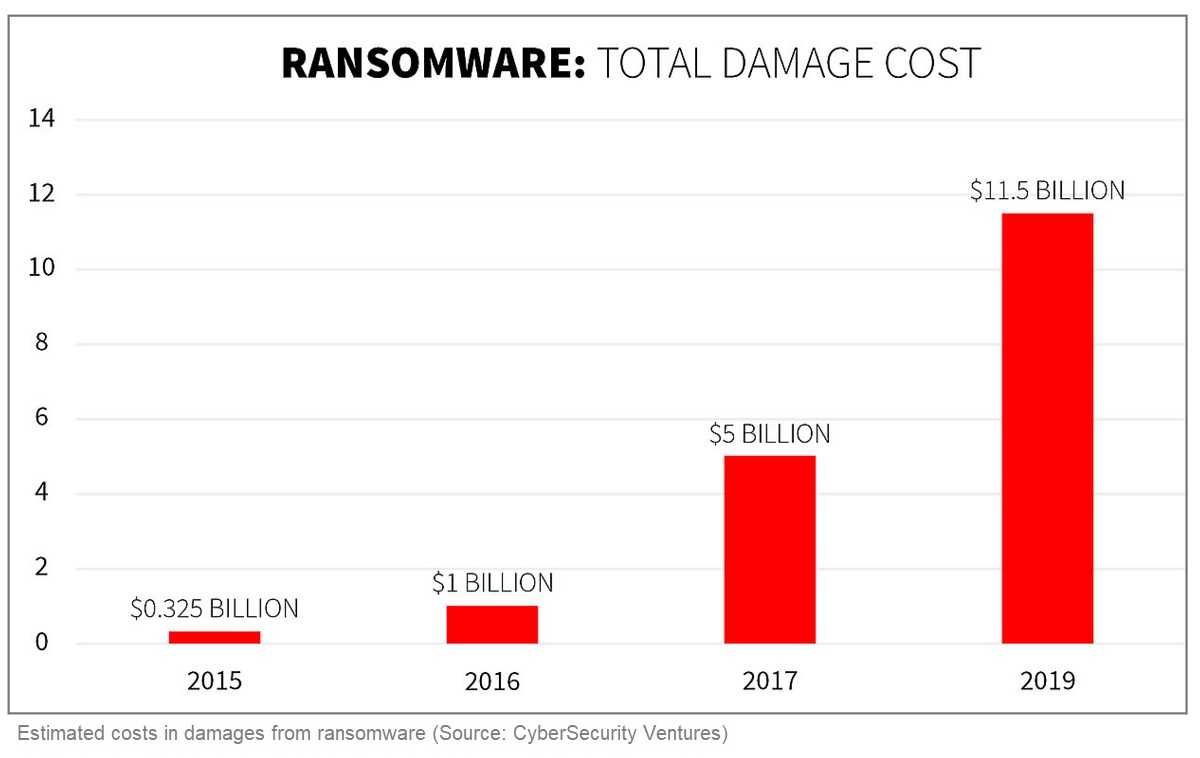
The FBI warns not to pay ransoms, as it will only encourage more attacks. However, for many small-to-medium-size businesses (SMB’s), having the resources for cyber-resilience is something many of them don’t have in the budget. Hackers know this too, and factor that in when choosing their ransom targets. When it comes to ransomware, hackers are counting on the volume of attacks–the more ransom demands likely to be paid add up to big bucks. The ransom amounts are never too high to be unthinkable, and are low enough to be quickly paid.
 Cybersecurity professionals agree the best defense against a ransom is a prepared offense. Those with the resources for backing-up data should absolutely do so, and the more sensitive the target–as with healthcare–the more frequent the back-ups should be. Restoring backed-up data needs to be tested, as even the most resilient back-up plans are useless if they don’t work properly.
Cybersecurity professionals agree the best defense against a ransom is a prepared offense. Those with the resources for backing-up data should absolutely do so, and the more sensitive the target–as with healthcare–the more frequent the back-ups should be. Restoring backed-up data needs to be tested, as even the most resilient back-up plans are useless if they don’t work properly.
Added to a back-up plan is the need to keep systems updated with the latest security patches. Hackers are continually finding ways to invade weaknesses in data systems and security patches help keep a weakness from becoming a tidal wave for ransomware.
For all the data defenses in place, employees continue to be the weakest link in cyber-resilience, most often as unsuspecting victims to email phishing. Training employees on cybersecurity, including robust attention to trending hacking and phishing tactics, is a very important link on the chain of cyber-resilience.