Credit and debit card skimming is nothing new to those who follow cybersecurity trends. The most common way we hear it used is with ATM cards. A device is installed on an ATM and as the cardholder inserts the card, information from the magnetic strip and the information entered into the keypad is recorded on the device. Ultimately, the criminal uses the information to empty the related account or make purchases. Recently, this same technology has been used on retailer sites in a similar way. No hardware is needed, however, and unlike being able to detect a device attached to an ATM, skimming on websites is invisible to the customer.
In 2018, many online retailers suffered such attacks on their sites. These included Ticketmaster, Newegg, and British Airways to name a few. Security professionals call this type of attack Magecart.
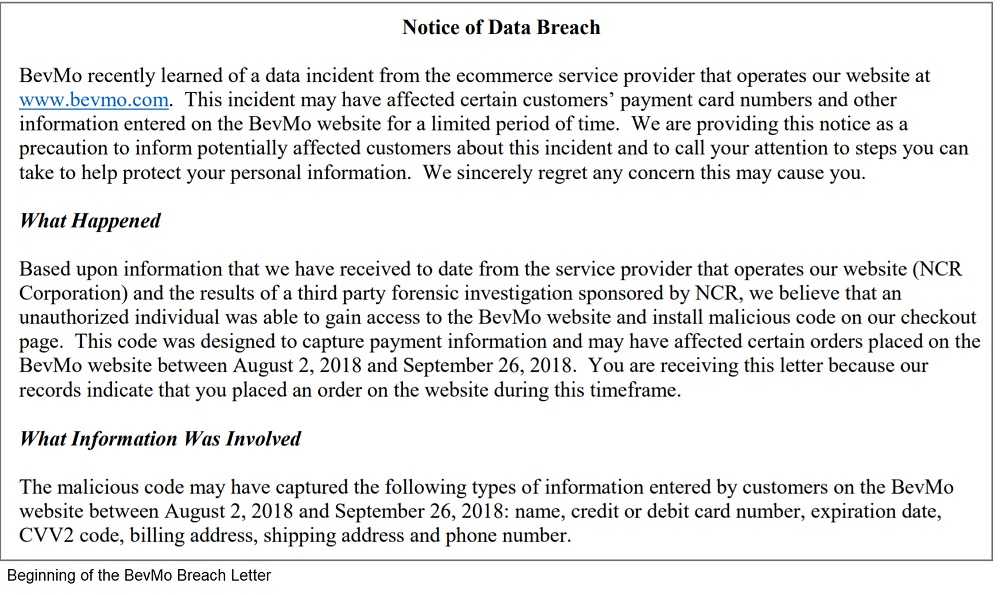
In these, malicious code is implanted on the websites that steals the payment card information as purchases are being made. A more recent attack that screams of Magecart was the beverage retailer, BevMo (Beverages and More). That one affected those who shopped on the website between August 2 and September 26, 2018. As of writing, the number of affected customers is not precisely reported, but ranges between 14,000 and 15,000. Notification letters were sent out to them on or around December 20.
 It hasn’t been documented precisely how Magecart got implanted on BevMo’s or other websites. However, there are two prime suspects. One is by exploiting a vulnerability in the web platform the site uses. Often, these machines are left unpatched, even after fixes are released. There are reasons a company may leave it unpatched, but it isn’t recommended that this be done. Known vulnerabilities just invite the criminals into the network, and in those cases they can really hurt. While costs can be calculated for removing the threat, for mailing out the notices to the victims, for legal fees, and other costs, the costs due to lower sales, loss in share price, and the harm to a company’s reputation cannot be easily quantified, nor can the reasons be easily determined. But it’s reasonable to assume some of that is because of the breach.
It hasn’t been documented precisely how Magecart got implanted on BevMo’s or other websites. However, there are two prime suspects. One is by exploiting a vulnerability in the web platform the site uses. Often, these machines are left unpatched, even after fixes are released. There are reasons a company may leave it unpatched, but it isn’t recommended that this be done. Known vulnerabilities just invite the criminals into the network, and in those cases they can really hurt. While costs can be calculated for removing the threat, for mailing out the notices to the victims, for legal fees, and other costs, the costs due to lower sales, loss in share price, and the harm to a company’s reputation cannot be easily quantified, nor can the reasons be easily determined. But it’s reasonable to assume some of that is because of the breach.
After hackers made it into Target’s point of sale system in 2013, the New York Times reported that the company saw loss in profits and a significant decline in share price. While it is difficult to prove it was because of the breach, it cannot be discounted.
Patching systems, whether you’re a large retailer or a small shop is equally important. While larger companies like BevMo can likely weather this storm, according to Small Business Trends, 60% of small businesses go out of business within six months of a data breach.
 The second way these breaches often happen is via phishing attacks. Phishing is usually perpetrated via email. Sometimes it’s spam; other times it’s very targeted. In either case, it’s important to keep staff and anyone that accesses your network and information aware of past and current phishing threats. This can be accomplished by creating a cybersecurity training and education strategy internally, or you can contract it out to one of several companies who perform these services. Whichever direction you choose make sure the program provides continual education as opposed to a once-per-year approach. Threats change day-to-day, so just providing this one time may mean missing important information.
The second way these breaches often happen is via phishing attacks. Phishing is usually perpetrated via email. Sometimes it’s spam; other times it’s very targeted. In either case, it’s important to keep staff and anyone that accesses your network and information aware of past and current phishing threats. This can be accomplished by creating a cybersecurity training and education strategy internally, or you can contract it out to one of several companies who perform these services. Whichever direction you choose make sure the program provides continual education as opposed to a once-per-year approach. Threats change day-to-day, so just providing this one time may mean missing important information.
So don’t wait to take steps to protect your organization. When you get a notification of a vulnerability, take it seriously. Apply the patches and keep staff and contractors aware of current risks and you can lower your risk of being the next victim of Magecart.