Instagram Scam Messages “Nasty List” Users
By: Jim Stickley and Tina Davis
July 29, 2019
It’s the moment that most happy Instagram fans become alarmed. A hacking scam targeting Instagram users involves receiving phishing messages warning them they are now on a “Nasty List.” Wait, what’s that? Yes, users receive a direct message from an account they are following, informing them about their debut on this dubious list. With Microsoft reporting phishing attacks skyrocketing by 250% in 2018, it should be enough to make all users, in this case those using Instagram, sit up and take notice.
Always one step ahead in a hacking scam, cybercriminals recently set their sights on Instagram. Scare tactics are a hacker’s calling card and those finding they are on this list are stepping right into a trap. Getting the unwelcome news about appearing on this list is followed by a link in the message. Following the link takes users to a fake Instagram login page that’s set up for the sole purpose of stealing their account credentials.
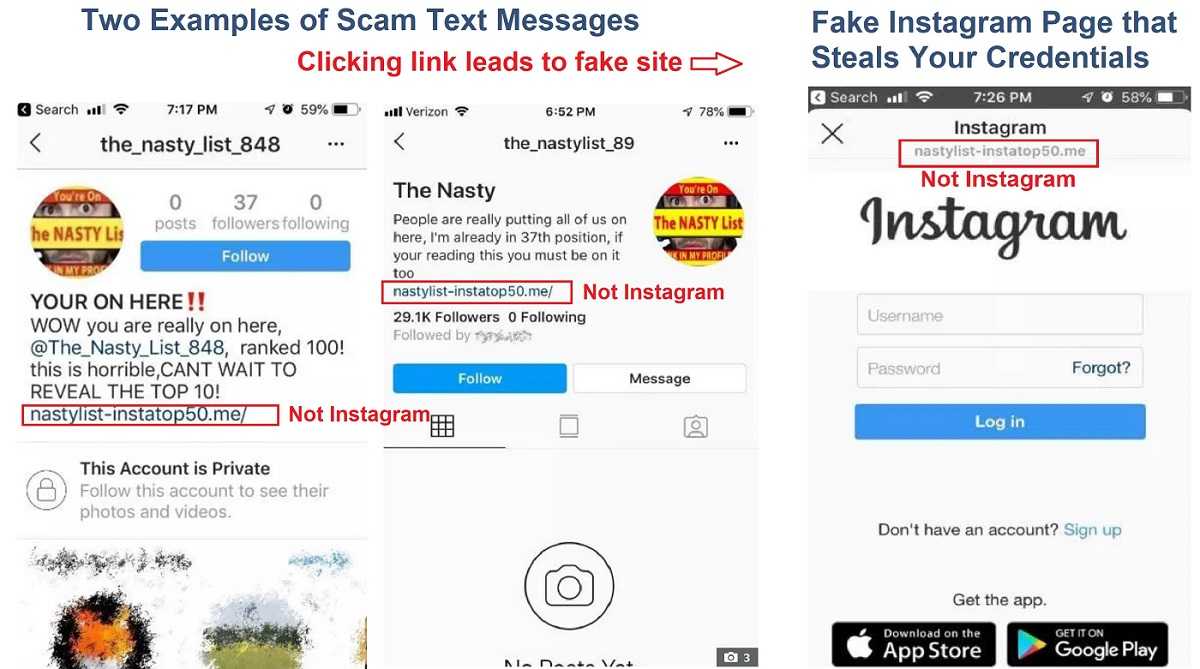
All messages include a link to the Nasty List with an explanation of why the user made the list. Once hackers have user information, they also steal contact lists and send similar Nasty List messages to them, spreading across the user’s social network like wildfire. Twitter users have posted screen shots of the scam, but for many on Instagram, it’s too little too late. Hackers love to harvest contact lists for targeting future scams. Those lists translate to hacker calling cards for phishing and other schemes yet to be determined or discovered, such as email spamming or malware attacks.
 No matter what ways hackers dream up to steal your data, there are common sense red flags many attacks have in common. Scare tactics or urgent-themed messages are a huge warning to think before acting. At best, these tactics are designed to steal something from users, be it contacts, logins, or account numbers. If it looks even slightly phishy, it’s time to delete it and move on, especially those emails containing links or attachments. Fake links are designed to steal data and attachments are likely filled with malware aimed at corrupting your device, possibly for even more diabolical attacks like ransomware.
No matter what ways hackers dream up to steal your data, there are common sense red flags many attacks have in common. Scare tactics or urgent-themed messages are a huge warning to think before acting. At best, these tactics are designed to steal something from users, be it contacts, logins, or account numbers. If it looks even slightly phishy, it’s time to delete it and move on, especially those emails containing links or attachments. Fake links are designed to steal data and attachments are likely filled with malware aimed at corrupting your device, possibly for even more diabolical attacks like ransomware.
Even though an odd or disturbing message may be from a contact, it’s easy to pick up a phone and verify the contact did or didn’t send it. Always enable two-factor authentication (2FA) whenever available. It adds an additional verification step for logins that gives hackers another roadblock to get to your account. 2FA also works with third-party authenticator apps. As users are often the front line of defense for cybercrimes, a healthy dose of suspicion can go a long way to cyber safety.