Just when you think it’s the biggest collection of breached data ever, another one comes along that’s even bigger. The security expert Troy Hunt wrote this week about a collection of data that shows nearly three-quarters of a million unique email address and password combinations that were posted in cloud storage ready for the taking. This means that if you think your email address has never been stolen before, it most likely has now.
Hunt, who runs the website Have I Been Pwned, was alerted to this collection. After cleaning it up, he came up with 772,904,9991 unique email addresses and 21,222, 975 unique passwords in this “Collection #1” of data. The name actually came from the dump of the data and is part of what leads him to believe it’s a combination of data from several breaches. He also found that much of it had already been in the Have I Been Pwned list, likely from other breaches such as LinkedIn from several years ago.
There are some steps you can take to prevent the reuse of your password if it appears in this collection…and it if isn’t in this group, it’s most likely in another group that can be found on Have I Been Pwned. Hackers reuse passwords to determine if they can get into other websites with them. It’s called “credential stuffing” and is relatively simple to do, with just a little bit of effort. Hunt has even posted YouTube videos of someone doing this and getting access to Spotify accounts with the stolen credentials; it’s rather shocking how elementary and efficient it is.
So, if you reuse any password on more than one website, no matter how unimportant you think the websites are or the data they store may be, change them to be unique. Follow strong password guidelines:
- At least eight characters
- Combine upper and lower caseletters
- Use numbers
- Use special characters
- Don’t make them dictionary words or proper names
- Don’t use personal information such as your birthdate or driver license number
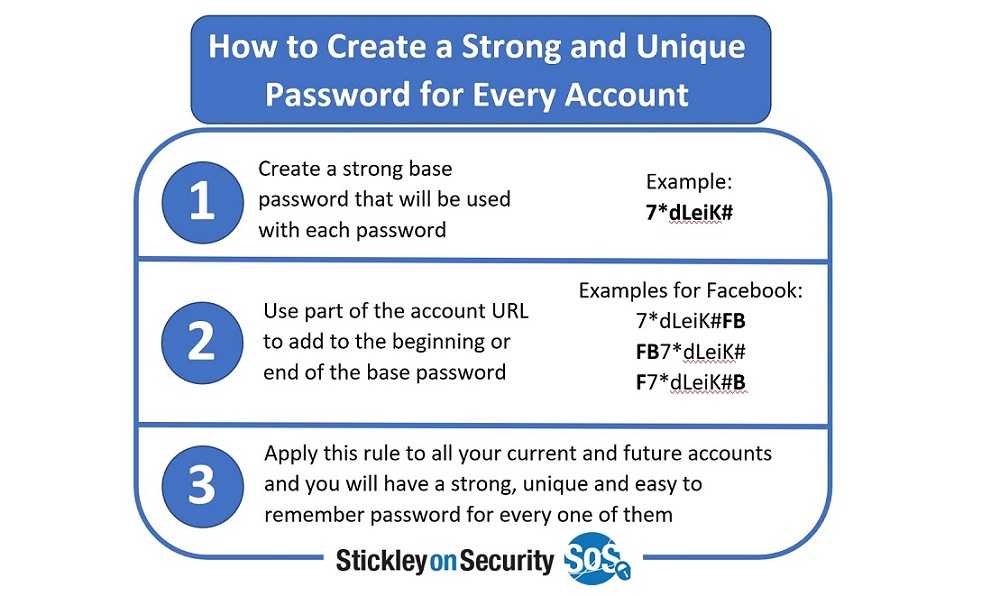
If you just cannot possibly remember all of your passwords, which is what generally leads someone to use the same one over and over, try a new strategy. Try creating a unique string of characters of at least six to use as your base password. Then make a new password for each website you visit using the name of the website and those six characters. For example, if you have an Amazon account (and who doesn’t these days), use “Xu%9T” as your base that is in every password and take the first two letters of the website name, “Am” and create “AXum%9T,” where the first and second characters of the site always go in the same location of your base password string. If you have a Yahoo account, it would be “YXua%9T.” The odds of repeating a password decrease immensely this way.
If you don’t want to do that, there is always the old pen and notebook strategy. Yes, writing them down is generally not recommended. However, it is unlikely that someone will get access to your notebook that you keep at home. Still, this is much better than reusing passwords.
A third option is to use a password manager. Just understand there is a risk of using these. They do generate random and unique passwords for your websites. However, you will need a “master” password to get access to the password manager. And if those sites get breached, whoever did that gets your master password. In fact, this has happened to LastPass and OneLogin in the past. That said, this is a far more secure strategy than reusing passwords on multiple websites.
Now, while some think this is the largest collection of data ever and recently posted, Brian Krebs of KrebsOnSecurity says otherwise. In fact, Krebs contacted the seller and said he was actually “steered” toward other, fresher data. Though the Collection #1 database was for sale at $45, making your password worth $.000002 to a hacker (Krebs did the math), but worth far more to you.
In any case, Krebs has the same advice about passwords and adds to use multifactor authentication (MFA) whenever possible. That is indeed a good tip.
The Collection #1 data has since been removed from the service where it was posted (the cloud service MEGA), but the damage was done. If you did use the same password on other sites, get to it and change them now.