Keeping up with the latest types of phishing scams can be a head-spinner. Well, move over phishing (email), spear phishing (targeted email), vishing (phone scams), and smishing (text messages), there’s a new kid on the block: Long Cast Phishing. According to cybersecurity specialist Professor John Walker, Long Cast Phishing is something everyone should be aware of. With all of the data breaches happening from small to mega-size, Long Cast Phishing refers to the long-term effects of being phished. After all, most of us have long-forgotten about those data breaches three years or even three months ago.
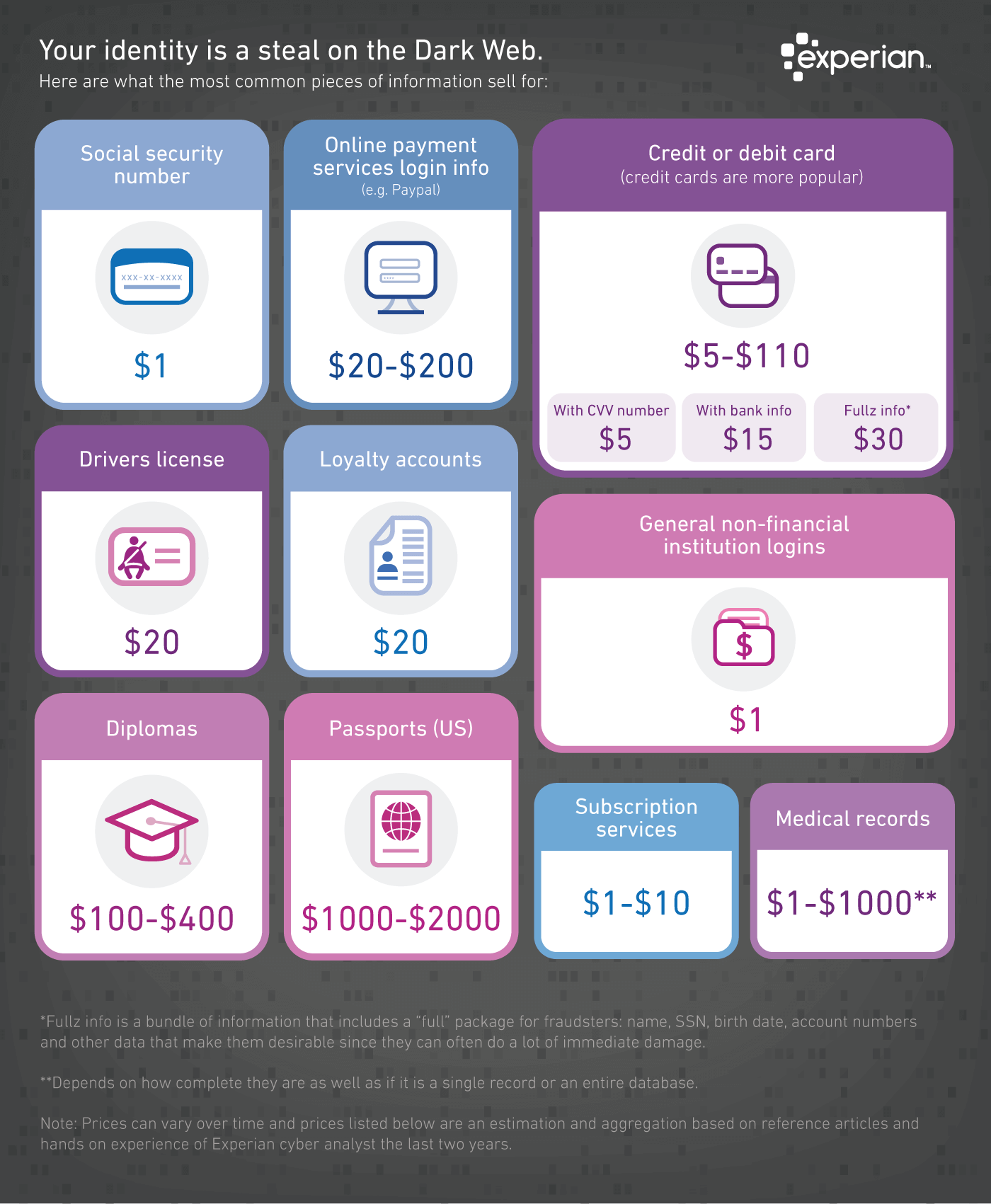
Professor Walker started with a theory that no matter which phishing tool was used to catch the bait, the repercussions of data theft last long after the original breach, which he calls Long Cast Phishing. He followed victims of various phishing attacks who supplied their personal data on phishing web sites or bogus documents. What he found was once information was entered, such as an email address, all types of phishing attacks continued to happen and even proliferate. Professor Walker surmised that stolen PII (Personally Identifiable Information) has extended value lasting long after the first phishing attack. Hackers know the value of each bit of PII, and selling it on the Dark Web provides ongoing misuse by those who purchase it and may then resell it to others for continued misuse.
Knowing your stolen data may have a very long shelf life with Long Cast Phishing, the need to protect your PII is more important than ever. Keeping aware of different phishing tactics is the best way to avoid them.
Email phishing: Don’t give them material for click bait. Hackers use anything and everything to get your attention, including topics of concern and fear. Remember, a hacker may have learned details about you on social media posts. When an email targets you using your name or a connection to your life, you’ve been spear-phished. Either way, immediately delete emails from unknown or suspicious senders. Should curiosity get the better of you and you open the email, do not under any circumstances download attachments or open links to other web sites. Chances are very good the attachments are loaded with malware, and the bogus web site is there to get your PII.
 Smishing: Hackers know texts to your mobile device must be short and powerfully motivating. For that reason, urgent texts from your financial institution about a serious matter could very well be smishing. If you receive one from your financial institution, take a minute to breathe. Call it with a number you have already saved or by searching for their services number on its website.
Smishing: Hackers know texts to your mobile device must be short and powerfully motivating. For that reason, urgent texts from your financial institution about a serious matter could very well be smishing. If you receive one from your financial institution, take a minute to breathe. Call it with a number you have already saved or by searching for their services number on its website.
Vishing: Beware phone calls from the IRS, your financial institution, or from someone offering you a fabulous prize. The IRS always contacts people through post office mail, and anything that sounds too good to be true is exactly that: too good to be true. True to email phishing attacks, vishing employs the same tactics by using the phone instead of email. Don’t hesitate to hang up. Should a caller say they represent your financial institution, hang up and call the bank directly using a trusted source for the phone number, such as from your monthly statement.
Remember that if any message tries to scare you into reacting quickly, you really just shouldn’t. Take a minute to think, contact the sender independently of the message received and get to the bottom of it that way. And never give personal or payment information to someone that claims to want to help you unless you initiated the contact in the first place.