We read the news to get…. well, news. But when the news can’t get to us, we start to wonder how, in this day and age, that happens. Over the final holiday weekend of 2018, Tribune Publishing left readers in quite a lurch when it couldn’t print their news. The culprit? Malware. Ransomware to be precise. It affected newspapers in Chicago, Connecticut, Florida, the Los Angeles Times, and the West Coast editions of the New York Times and the Wall Street Journal, as well as the San Diego Union-Tribune.
It was sports editors for the Union-Tribune that first experienced an issue. Although it is no longer owned by Tribune Publishing, they still share some systems. The editors were unable to transmit final pages to the printing facility, so work on figuring out what happened began.
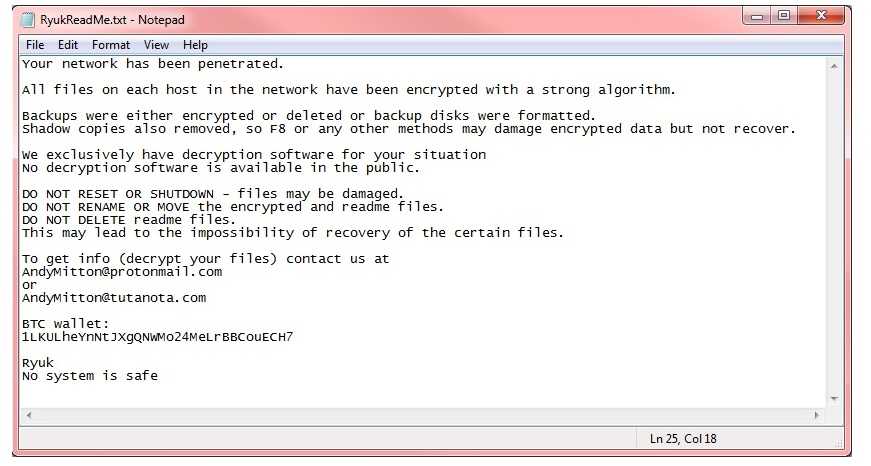
What is thought to have hit it was the ransomware Ryuk. A screenshot of a ransom note with the title RyukReadMe was obtained by the Los Angeles Times itself. It is a similar note to those in other Ryuk incidents. Oddly, though, no ransom amount was specified. The company did not state if any money or cryptocurrency was paid either. However, a spokesperson did say the issues were “largely resolved” by Monday.
In order to avoid your own news crisis, organizations should ensure that a multi-step cybersecurity process is in place. This should include:
 1. An ongoing training and awareness program to alert all users, including contractors and vendor users on current cybersecurity threats, especially with respect to phishing. Ransomware makes its way into a network in a variety of ways, but primarily it's found to be done via phishing. If everyone is aware of how to identify phishing and how to avoid it and report it, it can become a primary security barrier for your organization. Although it’s getting more difficult to detect, the signs are usually still there. These include typos and improper use of the language, incorrect logos, generic greetings, links that go to somewhere unexpected, an unexpected link or attachment is included in an email message, as well as other signs. Spending a few seconds to really read it, rather than panic, can help with this.
1. An ongoing training and awareness program to alert all users, including contractors and vendor users on current cybersecurity threats, especially with respect to phishing. Ransomware makes its way into a network in a variety of ways, but primarily it's found to be done via phishing. If everyone is aware of how to identify phishing and how to avoid it and report it, it can become a primary security barrier for your organization. Although it’s getting more difficult to detect, the signs are usually still there. These include typos and improper use of the language, incorrect logos, generic greetings, links that go to somewhere unexpected, an unexpected link or attachment is included in an email message, as well as other signs. Spending a few seconds to really read it, rather than panic, can help with this.
 2. Perform regular backups of important data. What is important and how often it gets backed up depends on what your organization does. Ransomware is increasingly common these days and security experts believe the criminals who use it will start targeting organizations that experience a critical situation if they don’t have access to the network or data. We saw a panic in 2017 when WannaCry spread to roughly 200,000 computers in 150 countries. It left companies such as Boeing, Honda, and the National Health Service in the UK in quite a lurch. In late 2018, it hit the Port of San Diego and the West Coasts’ 2nd largest port, the Port of Long Beach. Make sure to keep those backups separately from the production network and completely detached from the Internet if at all possible. Some ransomware, such as Zenis and SamSam, will seek out backup copies and encrypt those files too.
2. Perform regular backups of important data. What is important and how often it gets backed up depends on what your organization does. Ransomware is increasingly common these days and security experts believe the criminals who use it will start targeting organizations that experience a critical situation if they don’t have access to the network or data. We saw a panic in 2017 when WannaCry spread to roughly 200,000 computers in 150 countries. It left companies such as Boeing, Honda, and the National Health Service in the UK in quite a lurch. In late 2018, it hit the Port of San Diego and the West Coasts’ 2nd largest port, the Port of Long Beach. Make sure to keep those backups separately from the production network and completely detached from the Internet if at all possible. Some ransomware, such as Zenis and SamSam, will seek out backup copies and encrypt those files too.
 3. Patch your systems as soon as possible when a patch is released. Everyone is busy. We get it. But leaving your network systems unpatched just leaves the door open for any holes to be exploited. Take the time to get those applied to avoid giving the keys to your network to criminals.
3. Patch your systems as soon as possible when a patch is released. Everyone is busy. We get it. But leaving your network systems unpatched just leaves the door open for any holes to be exploited. Take the time to get those applied to avoid giving the keys to your network to criminals.
Ryuk is relatively new in the ransomware world. It was first seen in August of 2018. However, it’s definitely made a name for itself. Analysts at Check Point Research estimated that it already may have netted the hackers, which are thought to be linked to the same North Korean group behind WannaCry, about $640,000.