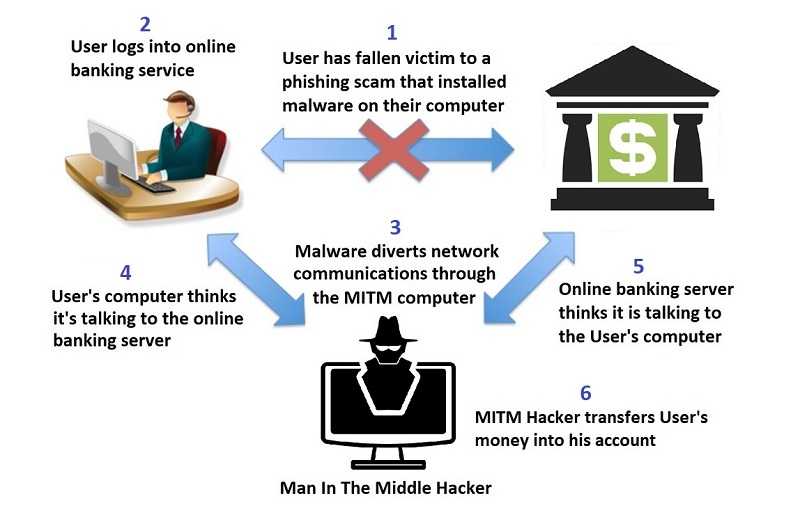
Some call it PandaBot. Others refer to it as Zeus Panda, but we here in the U.S. know it as the Panda Banker banking trojan. It’s on the move again and finding new targets. But what it’s trying to steal remains the same: Financial login credentials. It uses man-in-the-browser attacks as well as webinjects to be successful. More on those later.
One thing this version is not doing, is repeating any indicators of compromise (IOC) that were used in the past. So the anti-virus and other products that were able to find it in the past, won’t work anymore. That said, it doesn’t mean that’s it is a good idea to give up keeping all antivirus software updated. That is still important because as soon as a new version of malware is discovered, your software will get that information.
What it does mean is that everyone needs to be aware of how it gets onto your computer. Well that answer is getting more difficult to answer these days as there are so many ways criminals are now distributing malware. In the case of Panda Banker, criminals are using a variety of phishing emails that include malicious attachments or links that take people to a website that initiates a download. Below are three examples of active scams:
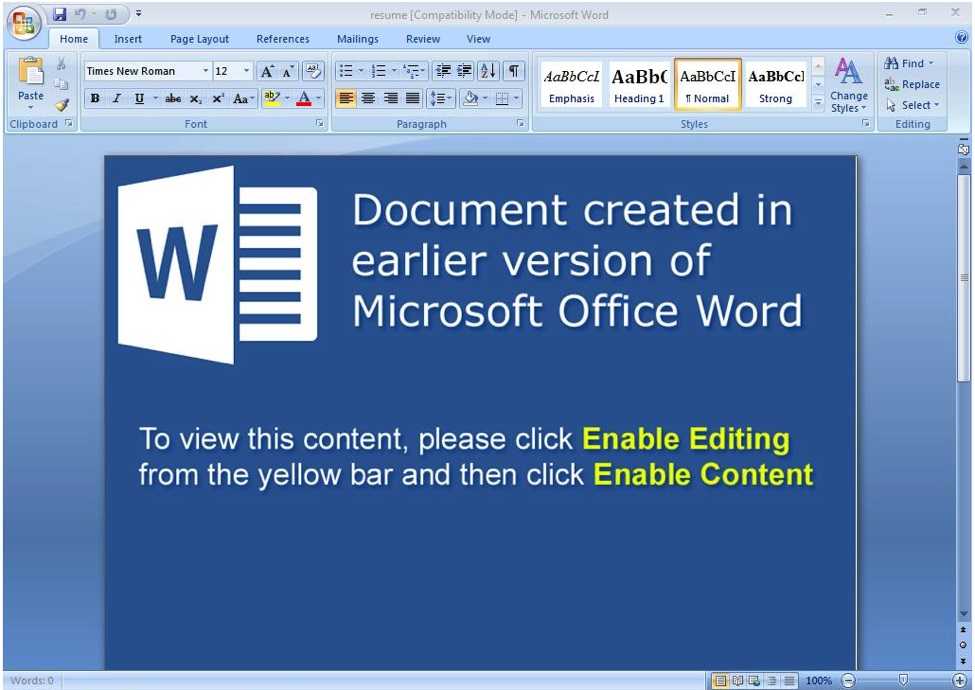
Figure 1: Fake resume document attachment contains macros that, if enabled, launch PowerShell code to download Zeus Panda (Source: Proofpoint)
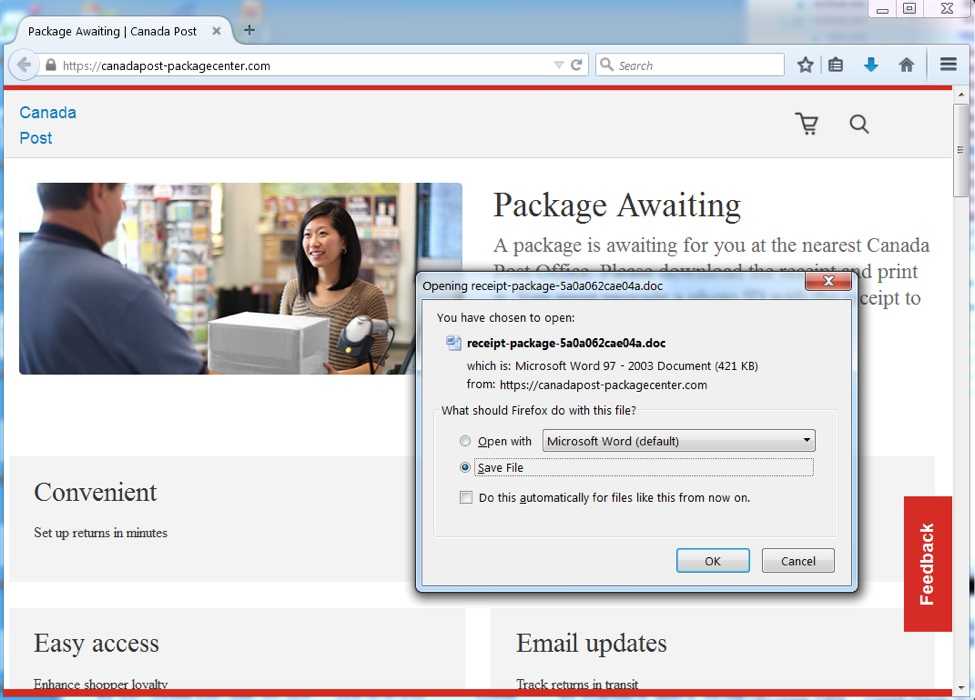
Figure 2: The malicious URLs redirect to another landing page, which in turns starts the document download (Source: Proofpoint)
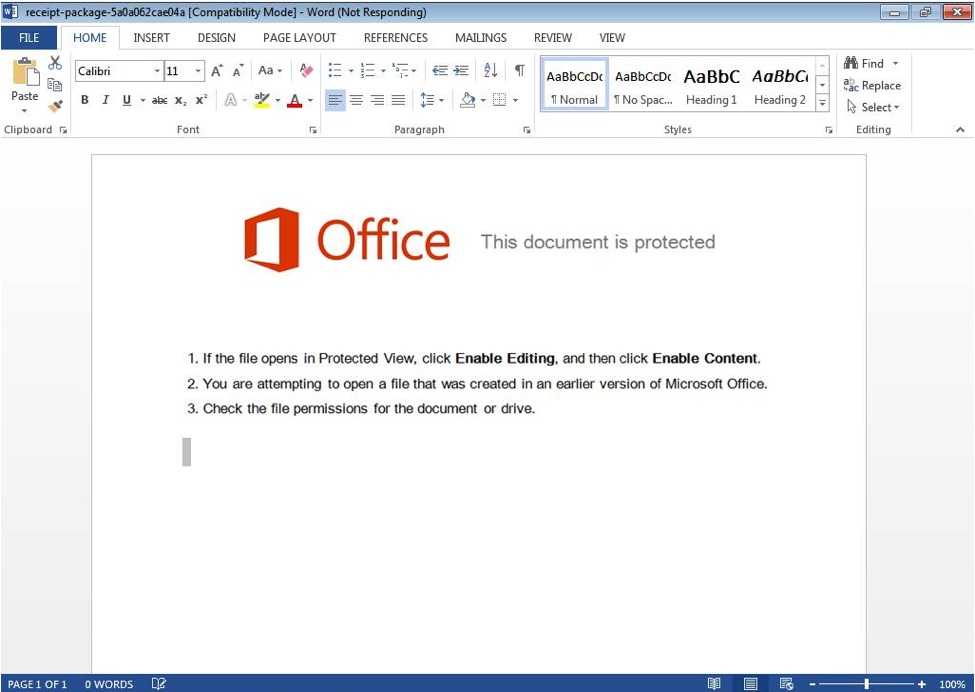
Figure 3: The malicious document receipt-package-5a0a062cae04a.doc contains macros that, if enabled, launched PowerShell code to download Zeus Panda (Source: Proofpoint)
Once installed, Panda Banker uses search words to determine when to activate. When it finds those related to banking and other sites, it will essentially “steal” your browser and trick you into providing information. This one is looking for certain sites in the following categories to activate:
 Sites having to do with payment cards
Sites having to do with payment cards- Web email sites
- Video search engine sites
- Search engines themselves, such as Bing or Yahoo!
- Online shopping sites
- Social media sites
- Adult content hubs
Once these identifiers are located by the malware, a man-in-the-browser attack takes place. Vulnerabilities in the browser are exploited allowing the attacker to modify web pages, transaction content, or to insert additional information to steal credentials. Basically, they make it appear that you’re entering your details into your financial institution’s site, for example, but really you’re just handing it over the bad actor. Unfortunately, it’s unlikely you will have any idea it’s happening.
Keep the browsers you use updated at all times. Some of them automatically update but may still need to be restarted for the update to take full effect. Others require more interaction from the user. Check on those specifics for what you use.
Malware such as this often make it into a system in the first place via phishing email. So always be on watch for those. It’s getting more difficult to determine what is real and what is not, so if you’re not expecting a link or attachment, don’t click it. Take a moment to call the sender to ensure it’s real. That can save you and your organization a lot of time and headaches.