Cybercriminals can be very crafty. Within the past couple of months, they have discovered a couple of new ways to fool Microsoft Office 365 Advanced Threat Protection (APT) anti-phishing capabilities. As reported by researchers at Avanan, both involve sending malicious links through email messages or by sending malicious attachments in email. And both should be considered serious.
The first is an exploitation of Microsoft’s Safe Links product. This feature checks URLs that arrive in email and compares them to a list of known malicious links or checks to see if it points to malware. If it does, the original link is replaced with an alert to the user that where they are about to go might harm them. Avanan calls the exploit of this baseStriker because of the way it takes advantage of how the headers in HTML messages read the “base” tag. It splits the URL so the Safe Links cannot detect the true link. Therefore, it gets past any filtering.
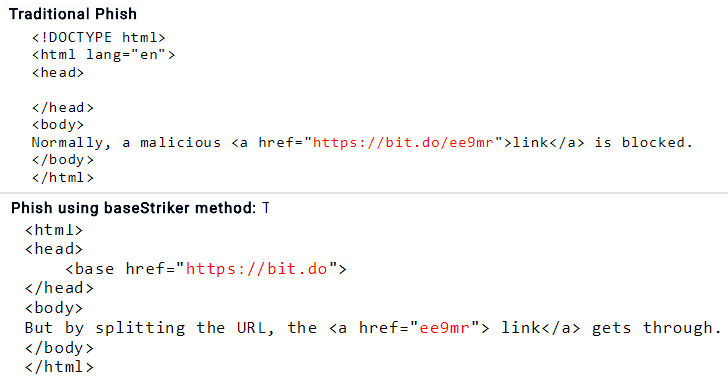
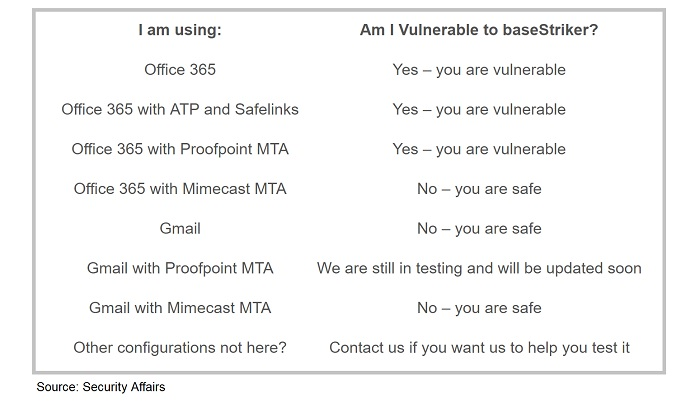
Security Affairs has tested different environments and offers the below advice:
The second way cybercriminals are getting aound Microsoft products is by manipulating font sizes. Office 365 uses natural language processing to determine if text in email may be potentially fraudulent or malicious. It does this by “reading” the text and if it sees a known name, such as “Apple” or “Microsoft,” but doesn’t come from a legitimate place, it will flag them. It also scans for words that coincide with user accounts, password resets, or financial related requests, among others.
The scammers are sending out phishing email messages with some of the text set to display in zero sized font. This means, the tools in Office 365 can’t properly process them and they make it through the filters.
An example Avanan provided was seeing the copyright notification for Microsoft. It may simply read “©2018 Microsoft Corporation.” When zero fonts are used within that phrase, it breaks up the name and the ATP cannot properly read it. So, the phrase could become “0h #$%!2 0ut of 18 Million Across Most of the Corporate World Have No Phish Protection,” with the bolded letters in the zero font. If the email gets past the filters and tools, it goes right into the user’s in box. Once there, there is a good chance the user will open it, especially if it seems customized to him or her.
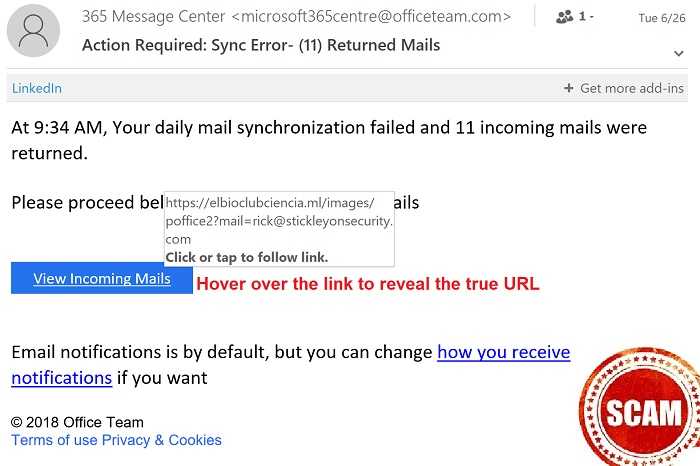
Remember that if you’re not expecting a link or attachment in your email, don’t just go clicking away. Verify it first, even if it looks like it’s meant just for you. Also, if the message tries to scare you in any way or elicit a reactionary response, stop, take a minute to think, and verify before clicking. If it comes in email, it can wait a few minutes for you to make sure you’re not unleashing malware on the network.
A common email being used with this ZeroFont method is the one that claims your email account is nearing the quota limit and your account will be unavailable to you if you don’t click a link to “upgrade” it. If you get such a message, contact your manager or IT department to validate it before taking action.