Chinese Backed Hacking Group Targets Big Pharma
By: Jim Stickley and Tina Davis
January 22, 2020
Yet another major pharmaceutical company fell victim to a hacking group believed to be sponsored by the Chinese government. Roche, a Swiss drug maker and diagnostics company, added its name to a long list of international companies targeted by the state-sponsored cybercriminals. Others caught in the group’s cross-hairs include Bayer, Marriott, Siemens, BASF, and Henkel. This attack is just one of many believed to be part of the Wicked Panda hacking group.
It’s well known that Chinese-backed hacking groups frequently target drug companies and those who do research for them. China has a particular interest in these companies as stealing their information helps support their own biomedical efforts. It’s far from the first time China has been accused of stealing intellectual property from Western countries to further their own goals.
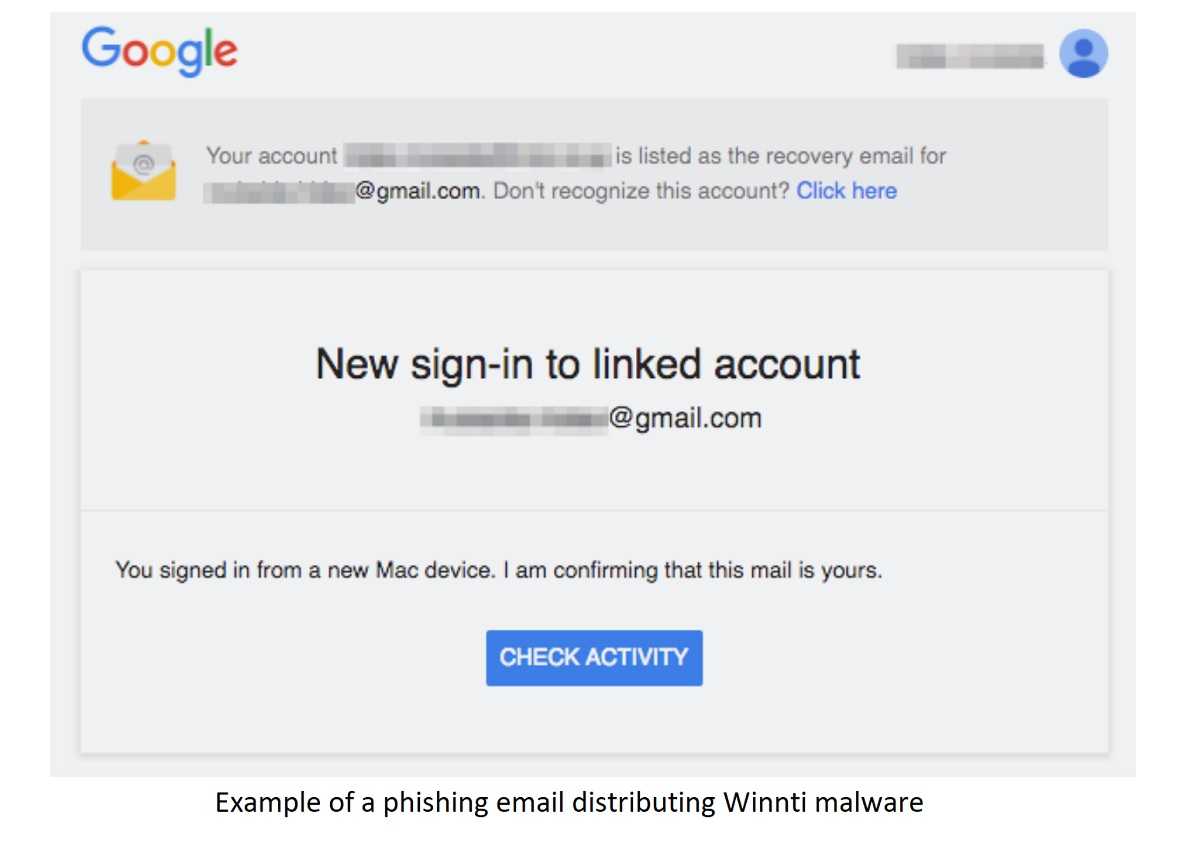
The Wicked Panda hackers use malware called Winnti that uses stolen security certificates to install the virus. After it enters a system, Winnti remotely runs malicious code on a victim’s device.
The hacking group dates back to 2010 when Winnti was used to go after online gaming companies. That use has since expanded over time to target international healthcare and commercial organizations. Experts call the malware attacks “highly sophisticated” and “well-resourced.”
Although all victims of Winnti claim no data was stolen or compromised, they believe the attackers copied their system data. Either way, the group now has the highly sensitive data of many international companies in its grasp. It’s no secret that malware enters a system through very sneaky tactics and it’s not only pharmaceutical companies, nor is this attack or others like it limited to China.
 Fortunately, there’s much a user can do to minimize the threat. With 66% of malware installed through infected email attachments, email phishing is a very real hazard. Since everyday users are the recipients of email phishing, cyber-education is the first line of defense in these attacks. Basic anti-phishing tactics go a long way helping a business and everyday users keep malware-free.
Fortunately, there’s much a user can do to minimize the threat. With 66% of malware installed through infected email attachments, email phishing is a very real hazard. Since everyday users are the recipients of email phishing, cyber-education is the first line of defense in these attacks. Basic anti-phishing tactics go a long way helping a business and everyday users keep malware-free.
- Never open an email attachment from an unknown source.
- Never follow links provided in an email. They can lead to fake websites designed to install malware and steal sensitive information.
- Phishing subject lines can appear urgent or too good to be true, so approach with caution.
- An email with bad grammar and incorrect spelling is a sure sign of a hacker.
- Keep devices current with the latest security patches and updates. They usually contain fixes for bugs and system flaws helping malware take root.
- Check a URL for typosquatting. Make sure it’s not slightly off, but close to the original and is being used to trick you into entering confidential information.