Enhanced MegaCortex Ransomware Means Business
By: Jim Stickley and Tina Davis
September 13, 2019
MegaCortex strains are the latest ransomware to hit business enterprise companies in the U.S. and Europe. The difference between this and other ransomware attacks is that MegaCortex v.2 clearly means business, big business. Their ransom demands to date are between $20,000 and $5.8 million to restore data, a huge departure from typical ransom demands. Hackers behind the malware make no apologies for the massive demands as they make clear in the ransom note that big profit is their motive. MegaCortex specifically targets business enterprise corporations–those who have the resources to pay the exorbitant ransom demands.
 “We are working for profit.”
“We are working for profit.”
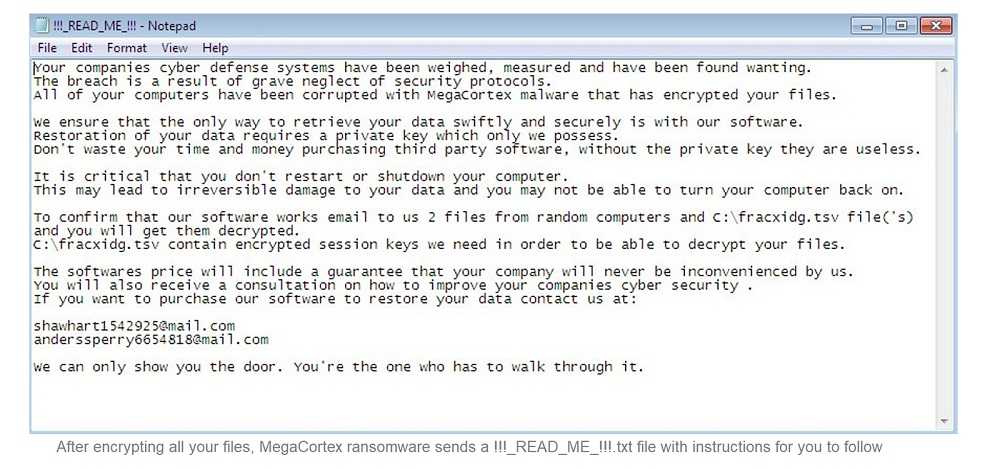
Those are just some of the alarming words contained in the hacker’s ransom note. This latest version of MegaCortex is modified to self-install its malicious code. Live password protections are stopped and altered to a hard-coded password that is difficult for system administrators to detect. These hard-coded passwords also let MegaCortex stop and kill antivirus protections along its route. With all these typical safety measures disabled, the ransomware has easy access to system data and encryption. The malware then encrypts data with an RSA public key.
The business enterprise victims of MegaCortex are chosen because of the substantial financial resources available to them. Paying a large ransom is feasible, and the ransomware takes advantage of that prospect. Previous ransomware attacks typically demand smaller ransoms but make up for the lower fee with an increase in the number of victims. MegaCortex victims also have the financial means for large cybersecurity budgets that can bolster data system protection. Considering this latest MegaCortex variant and how it works, enterprise business may choose to directly adjust system security to avoid infection. No enterprise wants to see the words used in the MegaCortex ransom note, “If you are reading this text, it means we’ve hacked your corporate network.”
News like this is always a good reminder to perform continual security and awareness training for all. Often, ransomware like this makes its way into a network via phishing. No matter how many perimeter security tools may be in place in any organization, all it takes is for one person to open an infected link or attachment in an email that slips by all those protections. The hackers who perform these attacks are no amateurs and will be thorough enough to find good targets. Training all year round on the latest threats and mitigation techniques is the best defense.