Financial Malware Attacks Up For Individuals And Business
By: Jim Stickley and Tina Davis
December 8, 2020
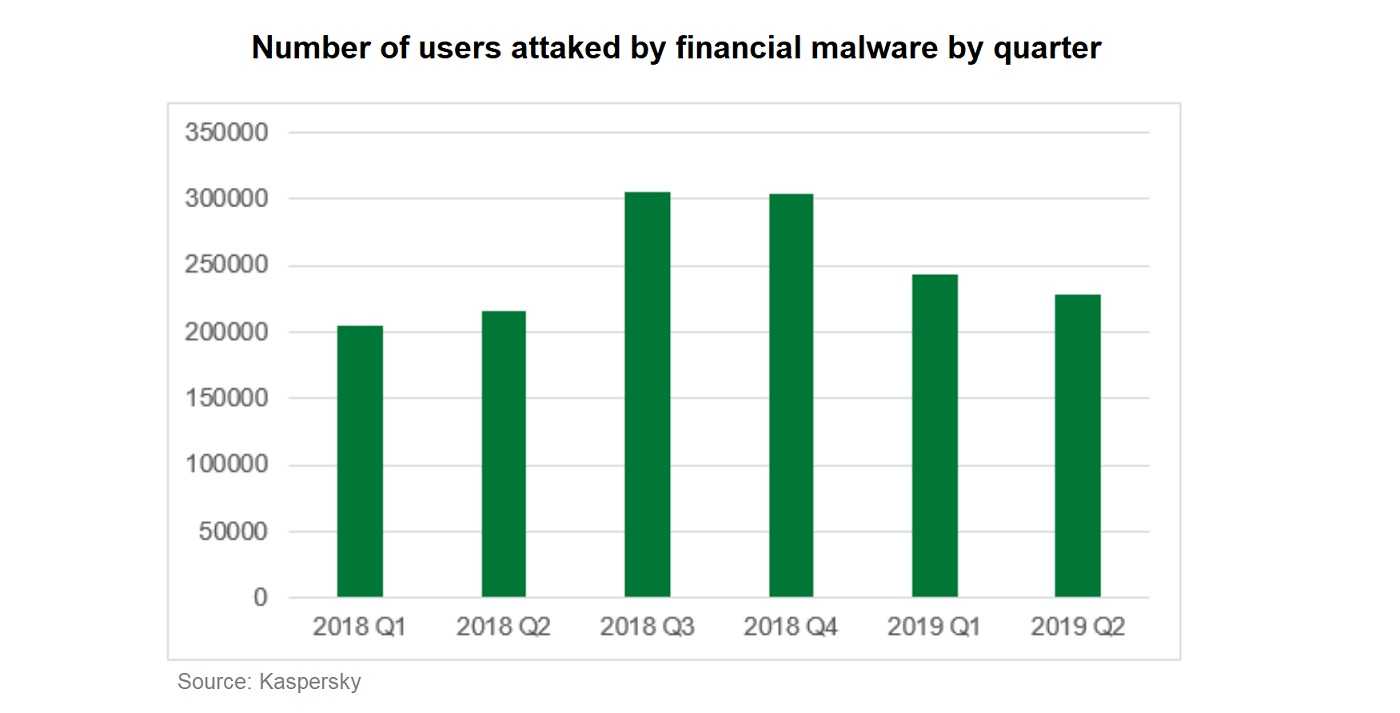
Financial malware attacks are on the rise. A recent Kaspersky report finds a 7% increase in those attacks targeting individual users and corporate finance. The uptick was discovered in the first half of 2019 and was compared to the same time period last year. The report finds a total of 430,000 users were targets of financial malware that hijacked banking information, cryptocurrencies, and other financial services. Corporate users made up 31% of the attacks compared to just 15% last year. The rise is a concern for both corporate and individual users who are concerned about being on the losing side of financial malware. The report finds the attacks also have something else in common–they both use email phishing and typosquatting to enter devices and systems.
Attacks targeting economic transactions are among the most lucrative. They provide a direct link to financial data including bank account numbers and passwords. In the report, the financial malware belongs to banking Trojan families. RTM Trojan first used in Russia, has since expanded globally and is now responsible for 40% of the attacks. Emotet Trojan, a malware responsible for 15% of attacks that take root in devices not updated with the latest security patches. The Trickster banking Trojan is responsible for 12% of attacks and is a credential-stealing malware. Once inside a system it quickly infects other devices. For individuals, Zbot malware is most the prominent financial malware, making up 26% of attacks. RTM came in second with nearly 25% and Emotet with 6.4% in the individuals category.
Understanding how financial malware enters systems tells us where we need to apply cybersecure measures. With email phishing and fake web pages as the gateway onto a device, individual and corporate users need to step-up anti-phishing awareness. This should be a continual process, not just a onetime per year approach. Threats change, so keeping employees on top of them is key.
 Spam emails and the links and attachments they include are a hacker’s calling card. Check email spam settings and choose a level that provides strong spam protection. Advise everyone connecting to the network not to act on links and attachments from unknown persons or that cannot be independently verified, or they don’t trust. Even if it appears to come from a colleague or friends, if it’s not expected, just don’t click it without picking up the phone and verifying. These days, even that isn’t a guarantee, so be 100% sure that what is beyond the link or inside the attachment in important to view.
Spam emails and the links and attachments they include are a hacker’s calling card. Check email spam settings and choose a level that provides strong spam protection. Advise everyone connecting to the network not to act on links and attachments from unknown persons or that cannot be independently verified, or they don’t trust. Even if it appears to come from a colleague or friends, if it’s not expected, just don’t click it without picking up the phone and verifying. These days, even that isn’t a guarantee, so be 100% sure that what is beyond the link or inside the attachment in important to view.
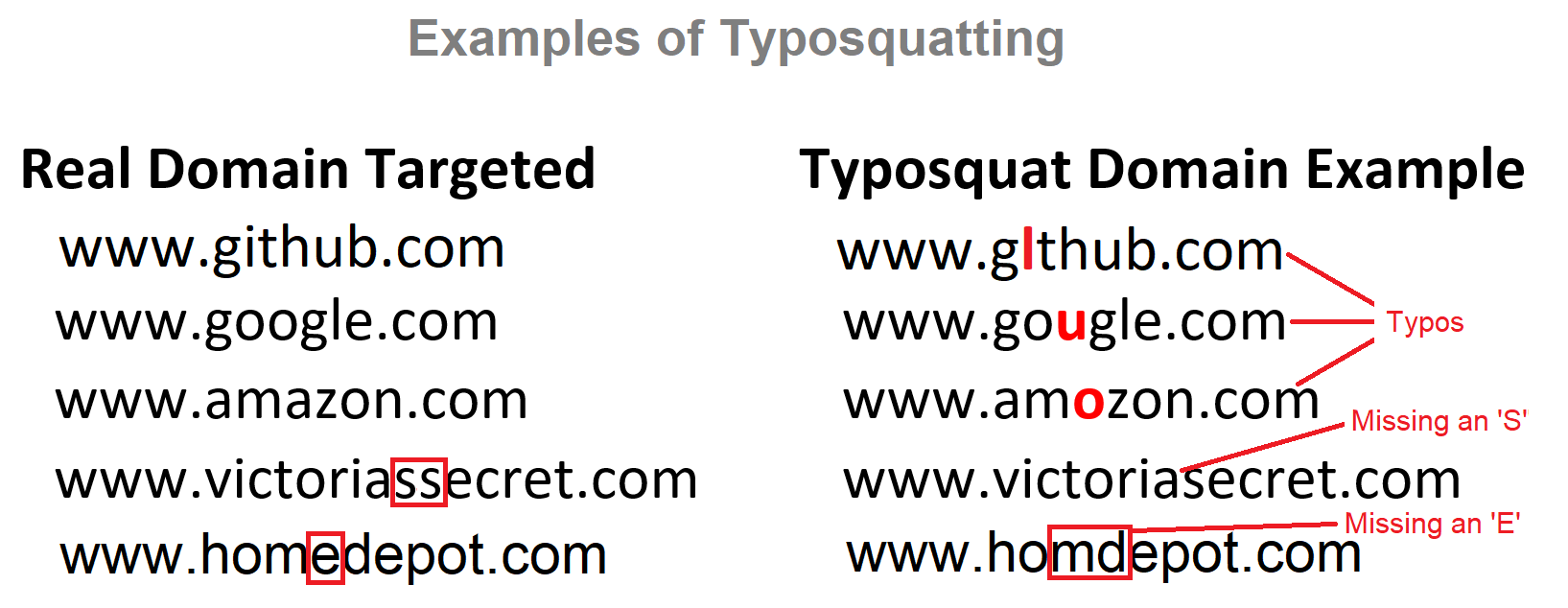
The increase in financial malware attacks also involves typosquatting web pages. Typosquatting works when bad actors sneakily misspell a URL, sending users to fake websites that are designed to steal their data. Typosquatting can be difficult to spot and paying careful attention to URL spelling goes a long way. The best cure for Typosquatting is always typing in the real URL yourself, rechecking it before clicking “Return,” and don’t trust links. Once you’re on the legitimate website you can check if your information is truly needed. Remember, always keep a device updated with the latest versions of apps and other software as soon as they’re available. These updates often include bug fixes and other security measures.