C-Suite Level Gives Hackers A Whale Of A Target
By: Jim Stickley and Tina Davis
March 26, 2019
Companies who are concerned with regular employees falling for hacks like phishing emails need to turn their attention a bit higher. Whaling attacks target those higher up on the corporate ladder. C-suite employees like CFO’s, COO’s, and CEO’s, along with upper management, are called “Whales” by hackers. This elite group is perfect prey for the discriminating hacker who goes right to decision makers instead of “smaller” rank-and-file employees. These corporate leaders need to be aware that they are human too, and just because they are further up the food chain does not mean they are immune from such attacks. It’s true, they should know better, but these whales are huge email phish food to hackers. It’s not just the little guys anymore.
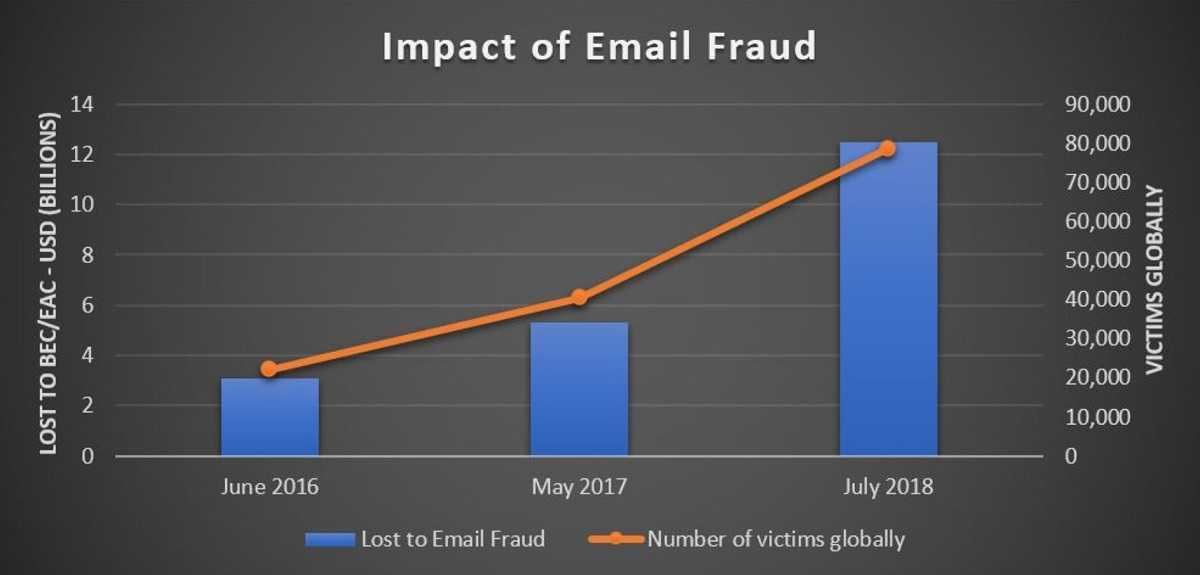
According to Forbes, in the past five years CFO’s of businesses around the world gave up more than $12 billion through socially engineered and business email compromise (BEC) attacks. They report that more than 50,000 CFO’s alone appear in databases targeted by cybercriminals and fraudsters. Those numbers don’t bode well for the rest of the C-level members, who report that 60-70% of CEO’s in the U.S. privately admit falling prey to whaling exploits.
Whales are usually the ones with control over the purse strings, and hackers take advantage of that. This includes sending phishing emails from a familiar vendor who needs payment immediately, to attempt personal extortion, or ransom of the individual whale. There are avenues for C-level whales to combat being targeted, including receiving the same cybersecurity education given to lower level employees. It’s a good idea to begin with cybersmart training and then expand to concerns involving finances and other duties.
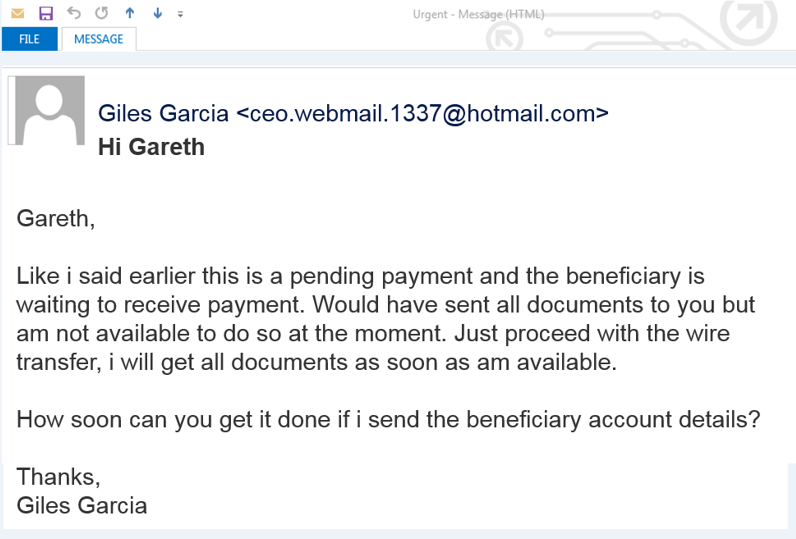
Don’t trust, and always verify, especially concerning wire-transfers. Alert the IT Department to any phishy emails, and never respond back to the email before doing so. An IT Department can investigate further and alert other employees to lookout for a particular suspected hack.
Always suspect any communication requiring a wire transfer and always require verification before any financial transfers occur. Pick up the phone if you have to and remember–a small inconvenience can prevent a massive attack.
Regardless of the amount, always require two separate verifications before sending money or sensitive information. Maintain a “Know Your Customers” (KYC) compliance policy toward regular clients and vendors. This policy always verifies recipients and requests before transfers of any kind are made.